Sharp Words about US Government Security
May 22, 2025
 No AI. Just a dinobaby who gets revved up with buzzwords and baloney.
No AI. Just a dinobaby who gets revved up with buzzwords and baloney.
On Monday (April 29, 2025), I am headed to the US National Cyber Crime Conference. I am 80, and I don’t do too many “in person” lectures. Heck, I don’t do too many lectures anymore period. A candidate for the rest home or an individual ready for a warehouse for the soon-to-die is a unicorn amidst the 25 to 50 year old cyber fraud, law enforcement professionals, and government investigators.
In my lectures, I steer clear of political topics. This year, I have been assigned a couple of topics which the NCCC organizers know attract a couple of people out of the thousand or so attendees. One topic concerns changes in the Dark Web. Since I wrote “Dark Web Notebook” years ago, my team and I keep track of what’s new and interesting in the world of the Dark Web. This year, I will highlight three or four services which caught our attention. The other topic is my current research project: Telegram. I am not sure how I became interested in this messaging service, but my team and I will will make available to law enforcement, crime analysts, and cyber fraud investigators a monograph modeled on the format we used for the “Dark Web Notebook.”
I am in a security mindset before the conference. I am on the lookout for useful information which I can use as a point of reference or as background information. Despite my age, I want to appear semi competent. Thus, I read “Signalgate Lessons Learned: If Creating a Culture of Security Is the Goal, America Is Screwed.” I think the source publication is British. The author may be an American journalist.
Several points in the write up caught my attention.
First, the write up makes a statement I found interesting:
And even if they are using Signal, which is considered the gold-standard for end-to-end chat encryption, there’s no guarantee their personal devices haven’t been compromised with some sort of super-spyware like Pegasus, which would allow attackers to read the messages once they land on their phones.
I did not know that Signal was “considered the gold standard for end-to-end chat encryption.” I wonder if there are some data to back this up.
Second, is NSO Group’s Pegasus “super spyware.” My information suggests that there are more modern methods. Some link to Israel but others connect to other countries; for example, Spain, the former Czech Republic, and others. I am not sure what “super” means, and the write up does not offer much other than a nebulous adjectival “super spyware.”
Third, these two references are fascinating:
“The Salt Typhoon and Volt Typhoon campaigns out of China demonstrate this ongoing threat to our telecom systems. Circumventing the Pentagon’s security protocol puts sensitive intelligence in jeopardy.”
The authority making the statement is a former US government official who went on to found a cyber security company. There were publicized breaches, and I am not sure comparable to Pegasus type of data exfiltration method. “Insider threats” are different from lousy software from established companies with vulnerabilities as varied as Joseph’s multi-colored coat. An insider, of course, is an individual presumed to be “trusted”; however, that entity provides information for money to an individual who wants to compromise a system, a person who makes an error (honest or otherwise), and victims who fall victim to quite sophisticated malware specifically designed to allow targeted emails designed to obtain information to compromise that person or a system. In fact, the most sophisticated of these “phishing” attack systems are available for about $250 per month for the basic version with higher fees associated with more robust crime as a service vectors of compromise.
The opinion piece seems to focus on a single issue focused on one of the US government’s units. I am okay with that; however, I think a slightly different angle would put the problem and challenge of “security” in a context less focused on ad hominin rhetorical methods.
Stephen E Arnold, May 22, 2025
Banks and Security? Absolutely
April 28, 2025
The second-largest US bank has admitted it failed to recover documents lost to a recent data breach. The Daily Hodl reports, “Bank of America Discloses Data Breach After Customers’ Documents Disappear, Says Names, Addresses, Account Information and Social Security Numbers Affected.” Writer Mark Emem tells us:
“Bank of America says efforts to locate sensitive documents containing personal information on an undisclosed number of customers have failed. The North Carolina-based bank says it is unable to recover the documents, which were lost in transit and ‘resulted in the disclosure’ of personal information. [The bank’s notice states,] ‘According to our records, the information involved in this incident was related to your savings bonds and included your first and last name, address, phone number, Social Security number, and account number…We understand how upsetting this can be and sincerely apologize for this incident and any concerns or inconvenience it may cause. We are notifying you so we can work together to protect your personal and account information.’”
Banks are forthcoming and bad actors know there is money in them. It is no surprise Bank of America faces a challenge. The succinct write-up notes the bank’s pledge to notify affected customers of any suspicious activity on their accounts. It is also offering them a two-year membership to an identity theft protection service. We suggest any Bank of America customers go ahead and change their passwords as a precaution. Now. We will wait.
Cynthia Murrell, April 28, 2025
Hey, We Know This Is Fake News: Sharing Secrets on Signal
April 24, 2025
Some government professionals allegedly blundered when they accidentally shared secret information via Signal with a reporter. The reporter, by the way, is not a person who wears a fedora with a command on it. To some, sharing close-hold information is an oopsie, but doing so with a non-hat wearing reporter is special. The BBC explained what the fallout will be from this mistake: “Why Is It A Problem If Yemen Strike Plans Shared On Signal?”
The Atlantic editor-in-chief Jeffrey Goldberg alleged received close-hold information via a free messaging application. A government professional seemed to agree that the messages appeared to be authentic. Hey, a free application is a cost reducer. Plus, Signal is believed to be encrypted end to end and super secure to boot. Signal is believed to be the “whisper network” of Washington D., an area known for its appropriate behavior and penchant for secrecy. (What was Wilbur Mills doing in the reflecting pool?)
While the messages are encrypted, bad actors (particularly those who may or may not be pals of the United States) allegedly can penetrate the Signal system. The Google Threat Intelligence Group noticed that Russia’s intelligence services have stepped up their hacking activities. Well, maybe or maybe not. Google is the leader in online advertising, but its “cyber security” expertise was acquired and may not be Googley yet.
The US government is not encouraging use of free messaging apps for sensitive information. That’s good. And the Pentagon is not too keen on a system not authorized to transmit non-public Department of Defense information. That’s good to know.
The whole sharing thing presents a potential downside for whomever is responsible for the misstep. The article says:
“Sensitive government communications are required to take place in a sealed-off room called a Sensitive Compartmentalized Information Facility (SCIF), where mobile phones are generally forbidden. The US government has other systems in place to communicate classified information, including the Joint Worldwide Intelligence Communications System (JWICS) and the Secret Internet Protocol Router (SIPR) network, which top government officials can access via specifically configured laptops and phones.”
Will there be consequences?
The article points out that the slip betwixt the cup and the lip may have violated two Federal laws:
“If confirmed, that would raise questions about two federal laws that require the preservation of government records: the Presidential Records Act and the Federal Records Act. "The law requires that electronic messages that take place on a non-official account are preserved, in some fashion, on an official electronic record keeping system," said Jason R Baron, a former director of litigation at the National Archives and Records Administration. Such regulations would cover Signal, he said.”
Hey, wasn’t the National Archive the agent interrupting normal business and holiday activities at a high profile resort residence in Florida recently? What does that outfit know about the best way to share sensitive information?
Whitney Grace, April 24, 2025
Israel Military: An Alleged Lapse via the Cloud
April 23, 2025
 No AI, just a dinobaby watching the world respond to the tech bros.
No AI, just a dinobaby watching the world respond to the tech bros.
Israel is one of the countries producing a range of intelware and policeware products. These have been adopted in a number of countries. Security-related issues involving software and systems in the country are on my radar. I noted the write up “Israeli Air Force Pilots Exposed Classified Information, Including Preparations for Striking Iran.” I do not know if the write up is accurate. My attempts to verify did not produce results which made me confident about the accuracy of the Haaretz article. Based on the write up, the key points seem to be:
- Another security lapse, possibly more severe than that which contributed to the October 2023 matter
- Classified information was uploaded to a cloud service, possibly Click Portal, associated with Microsoft’s Azure and the SharePoint content management system. Haaretz asserts: “… it [MSFT Azure SharePoint Click Portal] enables users to hold video calls and chats, create documents using Office applications, and share files.”
- Documents were possibly scanned using CamScanner, A Chinese mobile app rolled out in 2010. The app is available from the Russian version of the Apple App Store. A CamScanner app is available from the Google Play Store; however, I elected to not download the app.
Modern interfaces can confuse users. Lack of training rigor and dashboards can create a security problem for many users. Thanks, Open AI, good enough.
Haaretz’s story presents this information:
Officials from the IDF’s Information Security Department were always aware of this risk, and require users to sign a statement that they adhere to information security guidelines. This declaration did not prevent some users from ignoring the guidelines. For example, any user could easily find documents uploaded by members of the Air Force’s elite Squadron 69.
Regarding the China-linked CamScanner software, Haaretz offers this information:
… several files that were uploaded to the system had been scanned using CamScanner. These included a duty roster and biannual training schedules, two classified training presentations outlining methods for dealing with enemy weaponry, and even training materials for operating classified weapons systems.
Regarding security procedures, Haaretz states:
According to standard IDF regulations, even discussing classified matters near mobile phones is prohibited, due to concerns about eavesdropping. Scanning such materials using a phone is, all the more so, strictly forbidden…According to the Click Portal usage guidelines, only unclassified files can be uploaded to the system. This is the lowest level of classification, followed by restricted, confidential, secret and top secret classifications.
The military unit involved was allegedly Squadron 69 which could be the General Staff Reconnaissance Unit. The group might be involved in war planning and fighting against the adversaries of Israel. Haaretz asserts that other units’ sensitive information was exposed within the MSFT Azure SharePoint Click Portal system.
Several observations seem to be warranted:
- Overly complicated systems involving multiple products increase the likelihood of access control issues. Either operators are not well trained or the interfaces and options confuse an operator so errors result
- The training of those involved in sensitive information access and handling has to be made more rigorous despite the tendency to “go through the motions” and move on in many professionals undergoing specialized instruction
- The “brand” of Israel’s security systems and procedures has taken another hit with the allegations spelled out by Haaretz. October 2023 and now Squadron 69. This raises the question, “What else is not buttoned up and ready for inspection in the Israel security sector?
Net net: I don’t want to accept this write up as 100 percent accurate. I don’t want to point the finger of blame at any one individual, government entity, or commercial enterprise. But security issues and Microsoft seem to be similar to ham and eggs and peanut butter and jelly from this dinobaby’s point of view.
Stephen E Arnold, April 23, 2025
Oracle: Pricked by a Rose and Still Bleeding
April 15, 2025
How disappointing. DoublePulsar documents a senior tech giant’s duplicity in, “Oracle Attempt to Hide Serious Cybersecurity Incident from Customers in Oracle SaaS Service.” Blogger Kevin Beaumont cites reporting by Bleeping Computer as he tells us someone going by rose87168 announced in March they had breached certain Oracle services. The hacker offered to remove individual companies’ data for a price. They also invited Oracle to email them to discuss the matter. The company, however, immediately denied there had been a breach. It should know better by now.
Rose87168 responded by releasing evidence of the breach, piece by piece. For example, they shared a recording of an internal Oracle meeting, with details later verified by Bleeping Computer and Hudson Rock. They also shared the code for Oracle configuration files, which proved to be current. Beaumont writes:
“In data released to a journalist for validation, it has now become 100% clear to me that there has been cybersecurity incident at Oracle, involving systems which processed customer data. … All the systems impacted are directly managed by Oracle. Some of the data provided to journalists is current, too. This is a serious cybersecurity incident which impacts customers, in a platform managed by Oracle. Oracle are attempting to wordsmith statements around Oracle Cloud and use very specific words to avoid responsibility. This is not okay. Oracle need to clearly, openly and publicly communicate what happened, how it impacts customers, and what they’re doing about it. This is a matter of trust and responsibility. Step up, Oracle — or customers should start stepping off.”
In an update to the original post, Beaumont notes some linguistic slight-of-hand employed by the company:
“Oracle rebadged old Oracle Cloud services to be Oracle Classic. Oracle Classic has the security incident. Oracle are denying it on ‘Oracle Cloud’ by using this scope — but it’s still Oracle cloud services that Oracle manage. That’s part of the wordplay.”
However, it seems the firm finally admitted the breach was real to at least some users. Just not in in black and white. We learn:
“Multiple Oracle cloud customers have reached out to me to say Oracle have now confirmed a breach of their services. They are only doing so verbally, they will not write anything down, so they’re setting up meetings with large customers who query. This is similar behavior to the breach of medical PII in the ongoing breach at Oracle Health, where they will only provide details verbally and not in writing.”
So much for transparency. Beaumont pledges to keep investigating the breach and Oracle’s response to it. He invites us to follow his Mastodon account for updates.
Cynthis Murrell, April 15, 2025
The EU Rains on the US Cloud Parade
March 3, 2025
At least one European has caught on. Dutch blogger Bert Hubert is sounding the alarm to his fellow Europeans in the post, "It Is No Longer Safe to Move Our Governments and Societies to US Clouds." Governments and organizations across Europe have been transitioning systems to American cloud providers for reasons of cost and ease of use. Hubert implores them to prioritize security instead. He writes:
"We now have the bizarre situation that anyone with any sense can see that America is no longer a reliable partner, and that the entire large-scale US business world bows to Trump’s dictatorial will, but we STILL are doing everything we can to transfer entire governments and most of our own businesses to their clouds. Not only is it scary to have all your data available to US spying, it is also a huge risk for your business/government continuity. From now on, all our business processes can be brought to a halt with the push of a button in the US. And not only will everything then stop, will we ever get our data back? Or are we being held hostage? This is not a theoretical scenario, something like this has already happened."
US firms have been wildly successful in building reliance on their products around the world. So much so, we are told, that some officials would rather deny reality than switch to alternative systems. The post states:
"’Negotiating with reality’ is for example the letter three Dutch government ministers sent last week. Is it wise to report every applicant to your secret service directly to Google, just to get some statistics? The answer the government sent: even if we do that, we don’t, because ‘Google cannot see the IP address‘. This is complete nonsense of course, but it’s the kind of thing you tell yourself (or let others tell you) when you don’t want to face reality (or can’t)."
Though Hubert does not especially like Microsoft tools, for example, he admits Europeans are accustomed to them and have "become quite good at using them." But that is not enough reason to leave data vulnerable to "King Trump," he writes. Other options exist, even if they may require a bit of effort to implement. Security or convenience: pick one.
Cynthia Murrell, March 3, 2025
Researchers Raise Deepseek Security Concerns
February 25, 2025
What a shock. It seems there are some privacy concerns around Deepseek. We learn from the Boston Herald, “Researchers Link Deepseek’s Blockbuster Chatbot to Chinese Telecom Banned from Doing Business in US.” Former Wall Street Journal and now AP professional Byron Tau writes:
“The website of the Chinese artificial intelligence company Deepseek, whose chatbot became the most downloaded app in the United States, has computer code that could send some user login information to a Chinese state-owned telecommunications company that has been barred from operating in the United States, security researchers say. The web login page of Deepseek’s chatbot contains heavily obfuscated computer script that when deciphered shows connections to computer infrastructure owned by China Mobile, a state-owned telecommunications company.”
If this is giving you déjà vu, dear reader, you are not alone. This scenario seems much like the uproar around TikTok and its Chinese parent company ByteDance. But it is actually worse. ByteDance’s direct connection to the Chinese government is, as of yet, merely hypothetical. China Mobile, on the other hand, is known to have direct ties to the Chinese military. We learn:
“The U.S. Federal Communications Commission unanimously denied China Mobile authority to operate in the United States in 2019, citing ‘substantial’ national security concerns about links between the company and the Chinese state. In 2021, the Biden administration also issued sanctions limiting the ability of Americans to invest in China Mobile after the Pentagon linked it to the Chinese military.”
It was Canadian cybersecurity firm Feroot Security that discovered the code. The AP then had the findings verified by two academic cybersecurity experts. Might similar code be found within TikTok? Possibly. But, as the article notes, the information users feed into Deepseek is a bit different from the data TikTok collects:
“Users are increasingly putting sensitive data into generative AI systems — everything from confidential business information to highly personal details about themselves. People are using generative AI systems for spell-checking, research and even highly personal queries and conversations. The data security risks of such technology are magnified when the platform is owned by a geopolitical adversary and could represent an intelligence goldmine for a country, experts warn.”
Interesting. But what about CapCut, the ByteDance video thing?
Cynthia Murrell, February 25, 2025
Google and Personnel Vetting: Careless?
February 20, 2025
 No smart software required. This dinobaby works the old fashioned way.
No smart software required. This dinobaby works the old fashioned way.
The Sundar & Prabhakar Comedy Show pulled another gag. This one did not delight audiences the way Prabhakar’s AI presentation did, nor does it outdo Google’s recent smart software gaffe. It is, however, a bit of a hoot for an outfit with money, smart people, and smart software.
I read the decidedly non-humorous news release from the Department of Justice titled “Superseding Indictment Charges Chinese National in Relation to Alleged Plan to Steal Proprietary AI Technology.” The write up states on February 4, 2025:
A federal grand jury returned a superseding indictment today charging Linwei Ding, also known as Leon Ding, 38, with seven counts of economic espionage and seven counts of theft of trade secrets in connection with an alleged plan to steal from Google LLC (Google) proprietary information related to AI technology. Ding was initially indicted in March 2024 on four counts of theft of trade secrets. The superseding indictment returned today describes seven categories of trade secrets stolen by Ding and charges Ding with seven counts of economic espionage and seven counts of theft of trade secrets.
Thanks, OpenAI, good enough.
Mr. Ding, obviously a Type A worker, appears to have quite industrious at the Google. He was not working for the online advertising giant; he was working for another entity. The DoJ news release describes his set up this way:
While Ding was employed by Google, he secretly affiliated himself with two People’s Republic of China (PRC)-based technology companies. Around June 2022, Ding was in discussions to be the Chief Technology Officer for an early-stage technology company based in the PRC. By May 2023, Ding had founded his own technology company focused on AI and machine learning in the PRC and was acting as the company’s CEO.
What technology caught Mr. Ding’s eye? The write up reports:
Ding intended to benefit the PRC government by stealing trade secrets from Google. Ding allegedly stole technology relating to the hardware infrastructure and software platform that allows Google’s supercomputing data center to train and serve large AI models. The trade secrets contain detailed information about the architecture and functionality of Google’s Tensor Processing Unit (TPU) chips and systems and Google’s Graphics Processing Unit (GPU) systems, the software that allows the chips to communicate and execute tasks, and the software that orchestrates thousands of chips into a supercomputer capable of training and executing cutting-edge AI workloads. The trade secrets also pertain to Google’s custom-designed SmartNIC, a type of network interface card used to enhance Google’s GPU, high performance, and cloud networking products.
At least, Mr. Ding validated the importance of some of Google’s sprawling technical insights. That’s a plus I assume.
One of the more colorful items in the DoJ news release concerned “evidence.” The DoJ says:
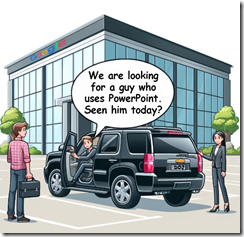
As alleged, Ding circulated a PowerPoint presentation to employees of his technology company citing PRC national policies encouraging the development of the domestic AI industry. He also created a PowerPoint presentation containing an application to a PRC talent program based in Shanghai. The superseding indictment describes how PRC-sponsored talent programs incentivize individuals engaged in research and development outside the PRC to transmit that knowledge and research to the PRC in exchange for salaries, research funds, lab space, or other incentives. Ding’s application for the talent program stated that his company’s product “will help China to have computing power infrastructure capabilities that are on par with the international level.”
Mr. Ding did not use Google’s cloud-based presentation program. I found the explicit desire to “help China” interesting. One wonders how Google’s Googley interview process run by Googley people failed to notice any indicators of Mr. Ding’s loyalties? Googlers are very confident of their Googliness, which obviously tolerates an insider threat who conveys data to a nation state known to be adversarial in its view of the United States.
I am a dinobaby, and I find this type of employee insider threat at Google. Google bought Mandiant. Google has internal security tools. Google has a very proactive stance about its security capabilities. However, in this case, I wonder if a Googler ever noticed that Mr. Ding used PowerPoint, not the Google-approved presentation program. No true Googler would use PowerPoint, an archaic, third party program Microsoft bought eons ago and has managed to pump full of steroids for decades.
Yep, the tell — Googlers who use Microsoft products. Sundar & Prabhakar will probably integrate a short bit into their act in the near future.
Stephen E Arnold, February 20, 2025
A Failure Retrospective
February 3, 2025
Every year has tech failures, some of them will join the zeitgeist as cultural phenomenons like Windows Vista, Windows Me, Apple’s Pippin game console, chatbots, etc. PC Mag runs down the flops in: “Yikes: Breaking Down the 10 Biggest Tech Fails of 2024.” The list starts with Intel’s horrible year with its booted CEO, poor chip performance. It follows up with the Salt Typhoon hack that proved (not that we didn’t already know it with TikTok) China is spying on every US citizen with a focus on bigwigs.
National Public Data lost 272 million social security numbers to a hacker. That was a great day in summer for hacker, but the summer travel season became a nightmare when a CrowdStrike faulty kernel update grounded over 2700 flights and practically locked down the US borders. Microsoft’s Recall, an AI search tool that took snapshots of user activity that could be recalled later was a concern. What if passwords and other sensitive information were recorded?
The fabulous Internet Archive was hacked and taken down by a bad actor to protest the Israel-Gaza conflict. It makes us worry about preserving Internet and other important media history. Rabbit and Humane released AI-powered hardware that was supposed to be a hands free way to use a digital assistant, but they failed. JuiceBox ended software support on its EV car chargers, while Scarlett Johansson’s voice was stolen by OpenAI for its Voice Mode feature. She sued.
The worst of the worst is this:
“Days after he announced plans to acquire Twitter in 2022, Elon Musk argued that the platform needed to be “politically neutral” in order for it to “deserve public trust.” This approach, he said, “effectively means upsetting the far right and the far left equally.” In March 2024, he also pledged to not donate to either US presidential candidate, but by July, he’d changed his tune dramatically, swapping neutrality for MAGA hats. “If we want to preserve freedom and a meritocracy in America, then Trump must win,” Musk tweeted in September. He seized the @America X handle to promote Trump, donated millions to his campaign, shared doctored and misleading clips of VP Kamala Harris, and is now working closely with the president-elect on an effort to cut government spending, which is most certainly a conflict of interest given his government contracts. Some have even suggested that he become Speaker of the House since you don’t have to be a member of Congress to hold that position. The shift sent many X users to alternatives like BlueSky, Threads, and Mastodon in the days after the US election.”
It doesn’t matter what Musk’s political beliefs are. He has no right to participate in politics.
Whitney Grace, February 3, 2025
National Security: A Last Minute Job?
January 20, 2025
On its way out the door, the Biden administration has enacted a prudent policy. Whether it will persist long under the new administration is anyone’s guess. The White House Briefing Room released a “Fact Sheet: Ensuring U.S. Security and Economic Strength in the Age of Artificial Intelligence.” The rule provides six key mechanisms on the diffusion of U.S. Technology. The statement specifies:
“In the wrong hands, powerful AI systems have the potential to exacerbate significant national security risks, including by enabling the development of weapons of mass destruction, supporting powerful offensive cyber operations, and aiding human rights abuses, such as mass surveillance. Today, countries of concern actively employ AI – including U.S.-made AI – in this way, and seek to undermine U.S. AI leadership. To enhance U.S. national security and economic strength, it is essential that we do not offshore this critical technology and that the world’s AI runs on American rails. It is important to work with AI companies and foreign governments to put in place critical security and trust standards as they build out their AI ecosystems. To strengthen U.S. security and economic strength, the Biden-Harris Administration today is releasing an Interim Final Rule on Artificial Intelligence Diffusion. It streamlines licensing hurdles for both large and small chip orders, bolsters U.S. AI leadership, and provides clarity to allied and partner nations about how they can benefit from AI. It builds on previous chip controls by thwarting smuggling, closing other loopholes, and raising AI security standards.”
The six mechanisms specify 18 key allies to whom no restrictions apply and create a couple trusted statuses other entities can attain. They also support cooperation between governments on export controls, clean energy, and technology security. As for “countries of concern,” the rule seeks to ensure certain advanced technologies do not make it into their hands. See the briefing for more details.
The measures add to previous security provisions, including the October 2022 and October 2023 chip controls. We are assured they were informed by conversations with stakeholders, bipartisan members of Congress, industry representatives, and foreign allies over the previous 10 months. Sounds like it was a lot of work. Let us hope it does not soon become wasted effort.
Cynthia Murrell, January 20, 2025