Honesty and Integrity? Are You Kidding Me?
April 23, 2025
 No AI, just the dinobaby himself.
No AI, just the dinobaby himself.
I read a blog post which begins with a commercial and self promotion. That allowed me to jump to the actual write up which contains a couple of interesting comments. The write up is about hiring a programmer, coder, or developer right now.
The write up is “Tech Hiring: Is This an Inflection Point?” The answer is, “Yes.” Okay, now what is the interesting part of the article? The author identifies methods of “hiring” which includes interviewing and determining expertise which no longer work.
These methods are:
- Coding challenges done at home
- Exercises done remotely
- Posting jobs on LinkedIn.
Why don’t these methods work?
The answer is, “Job applicants doing anything remotely and under self-supervision cheat. Okay, that explains the words “honesty” and “integrity” in the headline to my blog post.
It does not take a rocket scientist or a person who gives one lecture a year to figure out what works. In case you are wondering, the article says, “Real person interviews.” Okay, I understand. That’s the way getting a job worked before the remote working, Zoom interviews, and AI revolutions took place. Also, one must not forget Covid. Okay, I remember. I did not catch Covid, and I did not change anything about my work routine or daily life. But I did wear a quite nifty super duper mask to demonstrate my concern for others. (Keep in mind that I used to work at Halliburton Nuclear, and I am not sure social sensitivity was a must-have for that work.)
Several observations:
- Common sense is presented as a great insight. Sigh.
- Watching a live prospect do work yields high value information. But the observer must not doom scroll or watch TikToks in my opinion.
- Allowing the candidate to speak with other potential colleagues and getting direct feedback delivers another pick up truck of actionable information.
Now what’s the stand out observation in the self-promotional write up?
LinkedIn is losing value.
I find that interesting. I have noticed that the service seems to be struggling to generate interest and engagement. I don’t pay for LinkedIn. I am 80, and I don’t want to bond, interact, or share with individuals whom I will never meet in the short time I have left to bedevil readers of this Beyond Search post.
I think Microsoft is taking the same approach to LinkedIn that it has to the problem of security for its operating systems, the reliability of its updates, and the amazingly weird indifference to flaws in the cloud synchronization service.
That’s useful information. And, no, I won’t be attending the author’s one lecture a year, subscribing to his for fee newsletter, or listening to his podcast. Stating the obvious is not my cup of tea. But I liked the point about LinkedIn and the implications about honesty and integrity.
Stephen E Arnold, April 23, 2025
AI and Movies: Better and Cheaper!
April 21, 2025
 Believe it or not, no smart software. Just a dumb and skeptical dinobaby.
Believe it or not, no smart software. Just a dumb and skeptical dinobaby.
I am not a movie oriented dinobaby. I do see occasional stories about the motion picture industry. My knowledge is shallow, but several things seem to be stuck in my mind:
- Today’s movies are not too good
- Today’s big budget films are recycles of sequels, pre-quels, and less than equals
- Today’s blockbusters are expensive.
I did a project for a little-time B movie fellow. I have even been to an LA party held in a mansion in La Jolla. I sat in the corner in my brown suit and waited until I could make my escape.
End of Hollywood knowledge.
I read “Ted Sarandos Responds To James Cameron’s Vision Of AI Making Movies Cheaper: “There’s An Even Bigger Opportunity To Make Movies 10% Better.” No, I really did red the article. I cam away confused. Most of my pre-retirement work involved projects whose goal was to make a lot of money. The idea was be clever, do a minimum of “real” work, and then fix up the problems when people complained. The magic formula for some Silicon Valley and high-technology outfits located outside of the Plastic Fantastic World.
This article pits better versus cheaper. I learned:
Citing recent comments by James Cameron, Netflix Co-CEO Ted Sarandos said he hopes AI can make films “10% better,” not just “50% cheaper.”
Well, there you go. Better and cheaper. Is that the winning formula for creative work? The write up quotes Ted Sarandos (a movie expert, I assume) as saying:
Today, you can use these AI-powered tools to enable smaller-budget projects to have access to big VFX on screen.
From my point of view “better” means more VFX which is, I assume, movie talk for visual effects. These are the everyday things I see at my local grocery store. There are super heroes stopping crimes in progress. There are giant alien creatures shooting energy beams at military personnel. There are machines that have a great voice that some AI experts found particularly enchanting.
The cheaper means that the individuals who sit in front of computer screens fooling around with Blackmagic’s Fusion and the super-wonderful Adobe software will be able to let smart software do some of the work. If 100 people work on a big budget film’s VFX and smart software can do the work cheaper, the question arises, “Do we need these 100 people?” Based on my training, the answer is, “Nope. Let them find their future elsewhere.”
The article sidesteps two important questions: Question 1. What does better mean? Question 2. What does cheaper mean?
Better is subjective. Cheaper is a victim of scope creep. Big jobs don’t get cheaper. Big jobs get more expensive.
What smart software will do the motion picture industry is hasten its “re-invention.”
The new video stars are those who attract eyeballs on TikTok- and YouTube-type platforms. The traditional motion picture industry which created yesterday’s stars or “influencers” is long gone. AI is going to do three things:
- Replace skilled technicians with software
- Allow today’s “influencers” to become the next Clark Gabel and Marilyn Monroe (How did she die?)
- Reduce the barrier for innovations that do not come from recycling Superman-type pre-quels, sequels, and less than equals.
To sum up, both of these movie experts are right and wrong. I suppose both can be reskilled. Does Mr. Beast offer a for fee class on video innovation which includes cheaper production and better outputs?
Stephen E Arnold, April 21, 2025
When
YouTube: The Future Has Blown Its Horn
April 3, 2025
YouTube has come a long way in the last two decades. Google wants us to appreciate just how far, apparently. Digiday celebrates the occasion with the piece, "As YouTube Turns 20, Here Are the Numbers You Need to Know." Writer Krystal Scanlon shares several noteworthy statistics. For example, the company states, an average of 500 hours of video is uploaded to the platform every minute. On the other end of the equation, about 30,000 viewers visit the site each day, Neilsen reported in February 2024.
In fact, we learn, YouTube considers itself the "new television." That same Neilsen report shows the platform outperforming other major streaming services. (Though it only beat Netflix by a nose, at 9.2% of total TV usage to its 8.2%.) The platform happily monetizes those eyeballs the old-fashioned way, with ads. However, it has also enticed over 125 million users to at least try its subscription plans. As for content creators, about 500,000 of them have been at it for over 10 years. They must be getting enough out of it to stick around. But for how many that is a viable career and how many it is just a hobby the write-up does not say. Whatever the case, it is clear YouTube has creators to thank for its significant ad revenue. Scanlon writes:
"With Europe’s creator economy projected to reach $41.17 billion by 2030 and U.S. influencer marketing expected to grow 14.2% to $9.29 billion this year, according to eMarketer, it’s clear why YouTube is focused on staying ahead in the creator space. Part of that plan involves doubling down on YouTube’s ability to thrust creators into the cultural mainstream. Which is why the platform has said that creators are becoming the startups of Hollywood. Whether it’s scripting, editing behind the scenes or creators are hiring various staff as part of their new business — YouTube wants to be the launchpad."
Yes, that would be quite the get. It will have to fight certain other streaming services for that honor, we think. The post continues:
"YouTube contributed more than $45 billion to the U.S. GDP in 2023, according to Oxford Economics, and it created more than 430,000 full-time jobs. Similarly, in Europe, YouTube contributed €6.4 billion ($6.94 billion) to the EU’s GDP in 2023, according to the platform’s latest Impact report, not including the jobs created by the 100,000 creators in the region that have built their own businesses including hiring staff."
Here’s the kicker. As changes roil the Google search advertising approach, YouTube might be the Little Engine That Could for Googzilla. Next up? Google Advertising, Broadcast, and Cable. ABC?
Cynthia Murrell, April 3 2025
Amazon Twitches: Love That Streaming, Dontcha?
March 28, 2025
Having a pervasive online presence is great for business, especially if you’re an influencer and you want endorsements. There’s also a dark side to being in the public eye and that comes in the form of anything from home invasions to death threats. Twitch star Amouranth’s home was burgled and she ended up being assaulted. Three more female Twitch stars were in the danger zone. The BBC reports that, “Twitch Creators ‘Taking Live Stream Death Threats Very Seriously.”
Twitch stars Emiru, China, and Valkyrae received death threats from a follower named Russell. He appeared on their stream from Pacific Park, Santa Monica. He threatened to unalive [sic] Emiru when she refused to share her contact information. The streamers reported the incident to Santa Monica police.
Emiru, China, and Valkyrae have millions of followers online. They went to Santa Monica, rode some rides, and then they were followed by a bad actor. When he asked for Emiru’s contact information, she refused and he made the threat. The streamers were scared, so they screamed and ran into a store.
Some watchers said the streamers staged the incident. Valkyrae responded:
‘Posting on X, she also said what happened demonstrates the ‘harsh reality women live in’ and hit out at online comments that it was staged to drive hits.
‘Seeing accounts accusing my friends and I for faking this and blaming us instead of questioning the man’s behaviour has been embarrassing to see.
‘I’ve learned it doesn’t matter how much I accomplish in this industry or how much I try to gain respect, some men will hate women and blame women no matter the situation.’
Emiru did not appear in the follow-up stream on Monday but posted on X afterwards.
‘I wish I could say this was some kind of one-in-a-million incident, but the truth is, it is not,’ she said. ‘This is what life is like for girls.
‘I hope if anything, people see what happened and realise how much of a reality it is for women and content creators as a whole.’”
It’s horrible that these high profile streamers were accosted, received death threats, and were also accused of staging. It demonstrates what women in the public eye are incredibly vulnerable.
Whitney Grace, March 28, 2025
Amazon Twitch: Losing Social Traction of the Bezos Bulldozer
February 5, 2025
Twitch is an online streaming platform primarily used by gamers to stream their play seasons and interact with their fanbase. There hasn’t been much news about Twitch in recent months and it could be die to declining viewership. Tube Filter dives into the details with “Is Twitch Viewership At Its Lowest Point In Four Years?”
The article explains that Twitch had a total of 1.58 billion watch time hours in December 2024. This was its lowest month in four years according to Stream Charts. Twitch, however, did have a small increase in new streamers joining the platform and the amount of channels live at one time. Stream Charts did mention that December is a slow month due to the holiday season. Twitch is dealing with dire financial straits and made users upset when it used AI to make emotes.
Here are some numbers:
“In both October and November 2024, around 89,000 channels on average would be live on Twitch at any one time. In December, that figure pushed up to 92,392. Twitch also saw a bump in the overall number of active channels from 4,490,725 in November to 4,777,395 in December—a 6% increase. Streams Charts notes that all these streamers broadcasted a more diverse range of content of content than usual. “[I]t’s important to note that other key metrics for both viewer and streamer activity remain strong,” it wrote in a report about December’s viewership. “A positive takeaway from December was the variety of content on offer. Streamers broadcasted in 43,200 different categories, the highest figure of the year, second only to March.”
Twitch is also courting TikTok creators in case the US federal government bans the short video streaming platform. The platform has offerings that streamers want, but it needs to do more to attract more viewers. Changes have caused some viewers to pine for the days of Amouranth in her inflated kiddie pool, the extremely sensitive Kira, and the good old days of iBabyRainbow. Some even miss the live streaming gambling at home events.
Now what Amazon? Longer pre-roll advertisements? More opaque content guidelines? A restriction on fashion shows?
Whitney Grace, February 5, 2025
AI Video Is Improving: Hello, Hollywood!
December 30, 2024
Has AI video gotten scarily believable? Well, yes. For anyone who has not gotten the memo, The Guardian declares, “Video Is AI’s New Frontier—and It Is so Persuasive, We Should All Be Worried.” Writer Victoria Turk describes recent developments:
“Video is AI’s new frontier, with OpenAI finally rolling out Sora in the US after first teasing it in February, and Meta announcing its own text-to-video tool, Movie Gen, in October. Google made its Veo video generator available to some customers this month. Are we ready for a world in which it is impossible to discern which of the moving images we see are real?”
Ready or not, here it is. No amount of hand-wringing will change that. Turk mentions ways bad actors abuse the technology: Scammers who impersonate victims’ loved ones to extort money. Deepfakes created to further political agendas. Fake sexual images and videos featuring real people. She also cites safeguards like watermarks and content restrictions as evidence AI firms understand the potential for abuse.
But the author’s main point seems to be more philosophical. It was prompted by convincing fake footage of a tree frog, documentary style. She writes:
“Yet despite the technological feat, as I watched the tree frog I felt less amazed than sad. It certainly looked the part, but we all knew that what we were seeing wasn’t real. The tree frog, the branch it clung to, the rainforest it lived in: none of these things existed, and they never had. The scene, although visually impressive, was hollow.”
Turk also laments the existence of this Meta-made baby hippo, which she declares is “dead behind the eyes.” Is it though? Either way, these experiences led Turk to ponders a bleak future in which one can never know which imagery can be trusted. She concludes with this anecdote:
“I was recently scrolling through Instagram and shared a cute video of a bunny eating lettuce with my husband. It was a completely benign clip – but perhaps a little too adorable. Was it AI, he asked? I couldn’t tell. Even having to ask the question diminished the moment, and the cuteness of the video. In a world where anything can be fake, everything might be.”
That is true. An important point to remember when we see footage of a politician doing something horrible. Or if we get a distressed call from a family member begging for money. Or if we see a cute animal video but prefer to withhold the dopamine rush lest it turn out to be fake.
Cynthia Murrell, December 30, 2024
Google Meet: Going in Circles Is Either Brilliant or Evidence of a Management Blind Spot
October 24, 2024
 No smart software but we may use image generators to add some modern spice to the dinobaby’s output.
No smart software but we may use image generators to add some modern spice to the dinobaby’s output.
I read an article which seems to be a rhetorical semantic floor routine. “Google Meet (Original) Is Finally, Properly Dead” explains that once there was Google Meet. Actually there was something called Hangouts, which as I recall was not exactly stable on my steam powered system in rural Kentucky. Hangouts morphed into Hangouts Meet. Then Hangouts Meet forked itself (maybe Google forked its users?) and there was Hangouts Meet and Hangouts Chat. Hangouts Chat then became Google Chat.
The write up focuses on Hangouts Meet, which is now dead. But the write up says:
In April 2020, Google rebranded Hangouts Meet to just “Meet.” A couple of years later, in 2022, the company merged Google Duo into Google Meet due to Duo’s larger user base, aiming to streamline its video chat services. However, to avoid confusion between the two Meet apps, Google labeled the former Hangouts Meet as “Meet (Original)” and changed its icon to green. However, having two Google Meet apps didn’t make sense and the company began notifying users of the “Meet (Original)” app to uninstall it and switch to the Duo-rebranded Meet. Now, nearly 18 months later, Google is officially discontinuing the Meet (Original) app, consolidating everything and leaving just one version of Meet on the Play Store.
Got that? The article explains:
Phasing out the original Meet app is a logical move for Google as it continues to focus on developing and enhancing the newer, more widely used version of Meet. The Duo-rebranded Google Meet has over 5 billion downloads on the Play Store and is where Google has been adding new features. Redirecting users to this app aligns with Google’s goal of consolidating its video services into a single, feature-rich platform.
Let’s step back. What does this Meet tell us about Google’s efficiency? Here are my views:
- Without its monopoly money, Google could not afford the type of inefficiency evidenced by the tale of the Meets
- The product management process appears to operate without much, if any, senior management oversight
- Google allows internal developers to whack away, release services, and then flounder until a person decides, “Let’s try again, just with different Googlers.”
So how has that worked out for Google? First, I think Microsoft Teams is a deeply weird product. The Softies want Teams to have more functions than the elephantine Microsoft Word. But lots of companies use Word and they now use Teams. And there is Zoom. Poor Zoom has lost its focus on allowing quick and easy online video conferences. Now I have to hunt for options between a truly peculiar Zoom app and the even more clumsy Zoom Web site.
Then there is Google Meet Duo whatever. Amazing. The services are an example of a very confused dog chasing its tail. Round and round she goes until some adult steps in and says, “Down, girl, before you die.”
PS. Who Google Chats from email?
Stephen E Arnold, October 24, 2024
Canadians Unhappy about Tax on Streaming Video
August 15, 2024
Unfortunately the movie industry has tanked worldwide because streaming services have democratized delivery. Producers, directors, actors, and other industry professionals are all feeling the pain of tighter purse strings. The problems aren’t limited to Hollywood, because Morningstar explains that the US’s northern neighbor is also feeling the strain: “The Motion Picture Association-Canada Asks Canada Appeal Court To Stop Proposed Tax On Streaming Revenue.”
A group representing big entertainment companies: Walt Disney, Netflix, Warner Brothers, Discovery, Paramount Global, and more are asking a Canadian court to stop a law that would force the companies to pay 5% of their sales to the country to fund local news and other domestic content. The Motion Picture Association- Canada stated that tax from the Canadian Radio-television and Telecommunications Commission oversteps the organization’s authority. The group representing the Hollywood bigwigs also mentions that its clients spent billions in Canada every year.
The representative group are also arguing that the tax would force Canadian subscribers to pay more for streaming services and the companies might consider leaving the northern country. Canadian Radio-television and Telecommunications Commission countered that without the tax local content might not be made or distributed anymore. Hollywood’s lawyers doesn’t like it at all:
“In their filing with Canada’s Federal Court of Appeal, lawyers for the group say the regulator didn’t reveal “any basis” for why foreign streamers are required to contribute to the production of local television and radio newscasts. The broadcast regulator “concluded, without evidence, that ‘there is a need to increase support for news production,'” the lawyers said in their filing. ‘Imposing on foreign online undertakings a requirement to fund news production is not appropriate in the light of the nature of the services that foreign online undertakings provide.’”
Canada will probably keep the tax and Hollywood, instead of the executives eating the costs, will pass it onto consumers. Consumers will also be shafted, because their entertainment streaming services will continue to become expensive.
Whitney Grace, August 15, 2024
TV Pursues Nichification or 1 + 1 = Barrels of Money
July 10, 2024
 This essay is the work of a dumb dinobaby. No smart software required.
This essay is the work of a dumb dinobaby. No smart software required.
When an organization has a huge market like the Boy Scouts and the Girl Scouts? What do they do to remain relevant and have enough money to pay the overhead and salaries of the top dogs? They merge.
What does an old-school talking heads television channel do to remain relevant and have enough money to pay the overhead and salaries of the top dogs? They create niches.
A cheese maker who can’t sell his cheddar does some MBA-type thinking. Will his niche play work? Thanks, MSFT Copilot. How’s that Windows 11 update doing today?
Which path is the optimal one? I certainly don’t have a definitive answer. But if each “niche” is a new product, I remember hearing that the failure rate was of sufficient magnitude to make me a think in terms of a regular job. Call me risk averse, but I prefer the rational dinobaby moniker, thank you.
“CNBC Launches Sports Vertical amid Broader Biz Shift” reports with “real” news seriousness:
The idea is to give sports business executives insights and reporting about sports similar to the data and analysis CNBC provides to financial professionals, CNBC President KC Sullivan said in a statement.
I admit. I am not a sports enthusiast. I know some people who are, but their love of sport is defined by gambling, gambling and drinking at the 19th hole, and dressing up in Little League outfits and hitting softballs in the Harrod’s Creek Park. Exciting.
The write up held one differentiator from the other seemingly endless sports programs like those featuring Pat McAfee-type personalities. Here’s the pivot upon which the nichification turns:
The idea is to give sports business executives insights and reporting about sports similar to the data and analysis CNBC provides to financial professionals…
Imagine the legions of viewers who are interested in dropping billions on a major sports franchise. For me, it is easier to visualize sports betting. One benefit of gambling is a source of “addicts” for rehabilitation centers.
I liked the wrap up for the article. Here it is:
Between the lines: CNBC has already been investing in live coverage of sports, and will double down as part of the new strategy.
- CNBC produces an annual business of sports conference, Game Plan, in partnership with Boardroom.
- Andrew Ross Sorkin, Carl Quintanilla and others will host coverage from the 2024 Olympic Games in Paris this summer.
Zoom out: Cable news companies are scrambling to reimagine their businesses for a digital future.
- CNBC already sells digital subscriptions that include access to its live TV feed.
- In the future, it could charge professionals for niche insights around specific verticals, or beats.
Okay, I like the double down, a gambling term. I like the conference angle, but the named entities do not resonate with me. I am a dinobaby and nichification is not a tactic that an outfit with eyeballs going elsewhere makes sense to me. The subscription idea is common. Isn’t there something called “subscription fatigue”? And the plan to charge to access a sports portal is an interesting one. But if one has 1,000 people looking at content, the number who subscribe seems to be in the < one to two percent range based on my experience.
But what do I know? I am a dinobaby and I know about TikTok and other short form programming. Maybe that’s old hat too? Did CNBC talk to influencers?
Stephen E Arnold, July 10, 2024
Doom Scrolling Fixed by Watching Cheers Re-Runs
July 5, 2024
 This essay is the work of a dumb dinobaby. No smart software required.
This essay is the work of a dumb dinobaby. No smart software required.
I spotted an article which provided a new way to think about lying on a sofa watching reruns of “Cheers.” The estimable online news resource YourTango: Revolutionizing Your Relationships published “Man Admits he Uses TV to Heal His Brain from Endless Short-Form Content. And Experts Agree He’s onto Something.” Amazing. The vast wasteland of Newton Minnow has morphed into a brain healing solution. Does this sound like craziness? (I must admit the assertion seems wacky to me.) Many years ago in Washington, DC, there was a sports announcer who would say in a loud voice while on air, “Let’s go to the videotape.” Well, gentle reader, let’s go to the YourTango “real” news article.
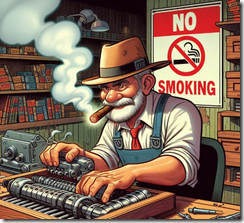
Will some of those mobile addicts and doom scrolling lovers take the suggestions of the YouTango article? Unlikely. The fellow with lung cancer continues to fiddle around, ignoring the No Smoking sign. Thanks, MSFT Copilot. How’s that Windows 11 update going?
The write up states:
A Gen Z man said he uses TV to ‘unfry’ his brain from endless short-form content — ‘Maybe I’ll fix the damage.’ It all feels so incredibly ironic that this young man — and thousands of other Gen Zers and millennials online — are using TV as therapy.
The individual who discovered this therapeutic use of OTA and YouTubeTV-type TV asserts:
I’m trying to unfry my brain from this short-form destruction.”
I admit. I like the phrase “short-form destruction.”
The write up includes this statement:
Not only is it keeping people from reading books, watching movies, and engaging in conversation, but it is also impacting their ability to maintain healthy relationships, both personal and professional. The dopamine release resulting from watching short-form content is why people become addicted to or, at the very least, highly attached to their screens and devices.
My hunch is that YourTango is not an online publication intended for those who regularly read the Atlantic and New Yorker magazines. That’s what makes these statement compelling. An online service for a specific demographic known to paw their mobile devices a thousand times or more each day is calling attention to a “problem.”
Now YourTango’s write up veers into the best way to teach. The write up states:
For young minds, especially kids in preschool and kindergarten, excessive screen time isn’t healthy. Their minds are yearning for connection, mobility, and education, and substituting iPad time or TV time isn’t fulfilling that need. However, for teenagers and adults in their 20s and 30s, the negative effects of too much screen time can be combated with a more balanced lifestyle. Utilizing long-form content like movies, books, and even a YouTube video could help improve cognitive ability and concentration.
The idea that watching a “YouTube video” can undo what flowing social media has done in the last 20 years is amusing to me. Really. To remediate the TikTok-type of mental hammering, one should watch a 10 minute video about the Harsh Trust of Big Automotive YouTube Channels. Does that sound effective?
Let’s look at the final paragraph in the “report”:
If you can’t read a book without checking your phone, catch a film without dozing off, or hold a conversation on a first date without allowing your mind to wander, consider some new habits that help to train your brain — even if it’s watching TV.
I love that “even if it’s watching TV.”
Net net: I lost attention after reading the first few words of the write up. I am now going to recognize my problem and watch a YouTube video called ”Dubai Amazing Dubai Mall. Burj Khalifa, City Center Walking Tour.” I feel less flawed just reading the same word twice in the YouTube video’s title. Yes. Amazing.
Stephen E Arnold, July 5, 2024