Soft Fraud: A Helpful List
July 18, 2024
 This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
For several years I have included references to what I call “soft fraud” in my lectures. I like to toss in examples of outfits getting cute with fine print, expiration dates for offers, and weasels on eBay asserting that the US Post Office issued a bad tracking number. I capture the example, jot down the vendor’s name, and tuck it away. The term “soft fraud” refers to an intentional practice designed to extract money or an action from a user. The user typically assumes that the soft fraud pitch is legitimate. It’s not. Soft fraud is a bit like a con man selling an honest card game in Manhattan. Nope. Crooked by design (the phrase is a variant of the publisher of this listing).
I spotted a write up called “Catalog of Dark Patterns.” The Hall of Shame.design online site has done a good job of providing a handy taxonomy of soft fraud tactics. Here are four of the categories:
- Privacy Zuckering
- Roach motel
- Trick questions
The Dark Patterns write up then populates each of the 10 categories with some examples. If the examples presented are not sufficient, a “View All” button allows the person interested in soft fraud to obtain a bit more color.
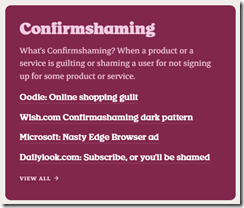
Here’s an example of the category “Confirmshaming”:
My suggestion to the Hall of Shame team is to move away from “too cute” categories. The naming might be clever, person searching for examples of soft fraud might not know the phrase “Privacy Zuckering.” Yes, I know that I have been guilty of writing phrases like the “zucked up,” but I am not creating a useful list. I am a dinobaby having a great time at 80 years of age.
Net net: Anyone interested in soft fraud will find this a useful compilation. Hopefully practitioners of soft fraud will be shunned. Maybe a couple of these outfits would be subject to some regulatory scrutiny? Hopefully.
Stephen E Arnold, July 18, 2024
Cloudflare, What Else Can You Block?
July 11, 2024
I spotted an interesting item in Silicon Angle. The article is “Cloudflare Rolls Out Feature for Blocking AI Companies’ Web Scrapers.” I think this is the main point:
Cloudflare Inc. today debuted a new no-code feature for preventing artificial intelligence developers from scraping website content. The capability is available as part of the company’s flagship CDN, or content delivery network. The platform is used by a sizable percentage of the world’s websites to speed up page loading times for users. According to Cloudflare, the new scraping prevention feature is available in both the free and paid tiers of its CDN.
Cloudflare is what I call an “enabler.” For example, when one tries to do some domain research, one often encounters Cloudflare, not the actual IP address of the service. This year I have been doing some talks for law enforcement and intelligence professionals about Telegram and its Messenger service. Guess what? Telegram is a Cloudflare customer. My team and I have encountered other interesting services which use Cloudflare the way Natty Bumpo’s sidekick used branches to obscure footprints in the forest.
Cloudflare has other capabilities too; for instance, the write up reports:
Cloudflare assigns every website visit that its platform processes a score of 1 to 99. The lower the number, the greater the likelihood that the request was generated by a bot. According to the company, requests made by the bot that collects content for Perplexity AI consistently receive a score under 30.
I wonder what less salubrious Web site operators score. Yes, there are some pretty dodgy outfits that may be arguably worse than an AI outfit.
The information in this Silicon Angle write up raises a question, “What other content blocking and gatekeeping services can Cloudflare provide?
Stephen E Arnold, July 11, 2024
Wow, Criticism from Moscow
June 17, 2024
 This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
I read “Edward Snowden Eviscerates OpenAI’s Decision to Put a Former NSA Director on Its Board: This Is a Willful, Calculated Betrayal of the Rights of Every Person on Earth.” The source is the interesting public figure Edward Snowden. He rose to fame by violating his secrecy requirement imposed by the US government on individuals with access to sensitive, classified, or top secret information. He then ended his dalliance with “truth” by relocating to Russia. From that bastion of truth and justice, he gives speeches and works (allegedly) at a foundation. He is a symbol of modern something. I find him a fascinating character, complete with the on-again, off-again glasses and his occasion comments about security. He is an expert on secrets it seems.
Thanks, MSFT Copilot.
Fortune Magazine obviously views him as a way to get clicks, sell subscriptions, and cement its position as a source of high-value business information. I am not sure my perception of Fortune is congruent with that statement. Let’s look and see what Mr. Snowden’s “news” is telling Fortune to tell us to cause me to waste a perfectly good Saturday (June 14, 2024) morning writing about an individual who willfully broke the law and decamped to that progressive nation state so believed by its neighbors in Eastern Europe.
Fortune reports:
“Do not ever trust OpenAI or its products,” the NSA employee turned whistleblower wrote on X Friday morning, after the company announced retired U.S. Army Gen. Paul Nakasone’s appointment to the board’s new safety and security committee. “There’s only one reason for appointing [an NSA director] to your board. This is a willful, calculated betrayal of the rights of every person on earth. You have been warned.”
Okay, I am warned. Several observations:
- Telegram, allegedly linked in financial and technical ways, to Russia recently began censoring the flow of information from Ukraine into Russia. Does Mr. Snowden have an opinion about that interesting development. Telegram told Tucker Carlson that it embraced freedom. Perhaps OpenAI is simply being pragmatic in the Telegram manner?
- Why should Mr. Snowden’s opinion warrant coverage in Fortune Magazine? Oh, sorry. I answered that already. Fortune wants clicks, money, and to be perceived as relevant. News flash: Publishing has changed. Please, tape the memo to your home office wall.
- Is Mr. Snowden correct? I am neither hot nor cold when it comes to Sam AI Man, the Big Dog at OpenAI. My thought is that OpenAI might be taking steps to understand how much value the information OpenAI can deliver to the US government once the iPhone magic moves from “to be” to reality. Most Silicon Valley outfits are darned clumsy in their response to warrants. Maybe OpenAI’s access to someone who knows interesting information can be helpful to the company and ultimately to its users who reside in the US?
Since 2013, the “Snowden thing” has created considerable ripples. If one accepts Mr. Snowden’s version of events, he is a hero. As such, shouldn’t he be living in the US, interacting with journalists directly not virtually, and presenting his views to the legal eagles who want to have a chat with him? Mr. Snowden’s response is to live in Moscow. It is okay in the spring and early summer. The rest of the year can be brutal. But there’s always Sochi for a much-needed vacay and the wilds of Siberia for a bit of prison camp exploration.
Moscow has its charms and an outstanding person like Mr. Snowden. Thanks, Fortune, for reminding me how important his ideas and laptop stickers are. I like the “every person on earth.” That will impress people in Latvia.
Stephen E Arnold, June 17, 2024
Think You Know Which Gen Z Is What?
June 7, 2024
 This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
I had to look this up? A Gen Z was born when? A Gen Z was born between 1981 and 1996. In 2024, a person aged 28 to 43 is, therefore, a Gen Z. Who knew? The definition is important. I read “Shocking Survey: Nearly Half of Gen Z Live a Double Life Online.” What do you know? A nice suburb, lots of Gen Zs, and half of these folks are living another life online. Go to one of those hip new churches with kick-back names and half of the Gen Zs heads bowed in prayer are living a double life. For whom do those folks pray? Hit the golf club and look at the polo shirt clad, self-satisfied 28 to 43 year olds. Which self is which? The chat room Dark Web person or a happy golfer enjoying the 19th hole?
Someone who is older is jumping to conclusions. Those vans probably contain office supplies, toxic waste, or surplus government equipment. No one would take Gen Zs out of the flow, would they? Thanks, MSFT. Do you have Gen Zs working on your superlative security systems?
The write up reports:
A survey of 2,000 Americans, split evenly by generation, found that 46% of Gen Z respondents feel their personality online vastly differs from how they present themselves in the real world.
Only eight percent of the baby boomers are different online. New flash: If you ever meet me, I am the same person writing these blog posts. As an 80-year-old dinobaby, I don’t need another persona to baffle the brats in the social media sewer. I just avoid the sewer and remain true to my ageing self.
The write up also provides this glimpse into the hearts and souls of those 28 to 43:
Specifically, 31% of Gen Z respondents admitted their online world is a secret from family
That’s good. These Gen Zs can keep a secret. But why? What are they trying to hide from their family, friends, and co-workers? I can guess but won’t.
If you work with a Gen Z, here’s an allegedly valid factoid from the survey:
53% of Gen Zers said it’s easier to express themselves online than offline.
Want another? Too bad. Here’s a winner insight:
68 percent of Gen Zs sometimes feel a disconnect between who they are online and offline.
I think I took a psychology class when I was a freshman in college. I recall learning about a mental disorder with inconsistent or contradictory elements. Are Gen Zs schizophrenic? That’s probably the wrong term, but I think I am heading in the right direction. Mental disorder signals flashing. Just the Gen Z I want to avoid if possible.
One aspect of the write up in the article is that the “author” — maybe human, maybe AI, maybe Gen X with a grudge, who knows? — is that some explanation of who paid the bill to obtain data from 2,000 people. Okay, who paid the bill? Answer: Lenovo. What company conducted the study? Answer: OnePoll. (I never heard of the outfit, and I am too much of a dinobaby to care much.)
Net net: The Gen Zs seem to be a prime source of persons of interest for those investigating certain types of online crime. There you go.
Stephen E Arnold, June 6, 2024
Telegram May Play a Larger Role In Future Of War And Education
June 4, 2024
 This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
Telegram is an essential tool for the future of crime. The Dark Web is still a hotbed of criminal activity, but as authorities crack down on it the bad actors need somewhere else to go. Stephen Arnold, Erik Arnold, et al. wrote a white paper titled E2EE: The Telegram Platform about how Telegram is replacing the Dark Web. Telegram is Dubai-based company with nefarious ties to Russia. The app offers data transfer for streaming audio and video, robust functions, and administrative tools. It’s being used to do everything from stealing people’s personal information to being an anti-US information platform.
The white paper details how Telegram is used to steal credit, gift, debit, and other card information. The process is called “carding” and a simple Google search reveals where stolen card information buyable. The team specifically investigated the Altenens.is, a paywall website to buy stolen information. It’s been removed from the Internet only to reappear again.
Altenens.is hosts forums, a chat, places to advertise products and services related to the website’s theme. Users are required to download and register with Telegram, because it offers encryption services for financial tractions. Altenen.is is only one of the main ways Telegram is used for bad acts:
“The Telegram service today is multi-faceted. One can argue that Telegram is a next-generation social network. Plus, it is a file transfer and rich media distribution service too. A bad actor can collect money from another Telegram user and then stream data or a video to an individual or a group. In the Altenen case example, the buyer of stolen credit cards gets a file with some carding data and the malware payload. The transaction takes place within Telegram. Its lax or hit-and-miss moderation method allows alleged illegal activity on the platform. ”
Telegram is becoming more advanced with its own cryptocurrency and abilities to mask and avoid third-party monitors. It’s used as a tool for war propaganda, but it’s also used to eschew authoritarian governments who want to control information. It’s interesting and warrants monitoring. If you work in an enforcement agency or a unit of the US government, you can request a copy of the white paper by writing benkent2020 @ yahoo dot com. Please, mention Beyond Search in your request. We do need to know your organization and area of interest.
Whitney Grace, June 4, 2024
Encryption Battles Continue
June 4, 2024
 This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
Privacy protections are great—unless you are law-enforcement attempting to trace a bad actor. India has tried to make it easier to enforce its laws by forcing messaging apps to track each message back to its source. That is challenging for a platform with encryption baked in, as Rest of World reports in, “WhatsApp Gives India an Ultimatum on Encryption.” Writer Russell Brandom tells us:
“IT rules passed by India in 2021 require services like WhatsApp to maintain ‘traceability’ for all messages, allowing authorities to follow forwarded messages to the ‘first originator’ of the text. In a Delhi High Court proceeding last Thursday, WhatsApp said it would be forced to leave the country if the court required traceability, as doing so would mean breaking end-to-end encryption. It’s a common stance for encrypted chat services generally, and WhatsApp has made this threat before — most notably in a protracted legal fight in Brazil that resulted in intermittent bans. But as the Indian government expands its powers over online speech, the threat of a full-scale ban is closer than it’s been in years.”
And that could be a problem for a lot of people. We also learn:
“WhatsApp is used by more than half a billion people in India — not just as a chat app, but as a doctor’s office, a campaigning tool, and the backbone of countless small businesses and service jobs. There’s no clear competitor to fill its shoes, so if the app is shut down in India, much of the digital infrastructure of the nation would simply disappear. Being forced out of the country would be bad for WhatsApp, but it would be disastrous for everyday Indians.”
Yes, that sounds bad. For the Electronic Frontier Foundation, it gets worse: The civil liberties organization insists the regulation would violate privacy and free expression for all users, not just suspected criminals.
To be fair, WhatsApp has done a few things to limit harmful content. It has placed limits on message forwarding and has boosted its spam and disinformation reporting systems. Still, there is only so much it can do when enforcement relies on user reports. To do more would require violating the platform’s hallmark: its end-to-end encryption. Even if WhatsApp wins this round, Brandom notes, the issue is likely to come up again when and if the Bharatiya Janata Party does well in the current elections.
Cynthia Murrell, June 4, 2024
Telegram: No Longer Just Mailing It In
May 29, 2024
 This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
Allegedly about 900 million people “use” Telegram. More are going to learn about the platform as the company comes under more European Union scrutiny, kicks the tires for next-generation obfuscation technology, and become a best friend of Microsoft… for now. “Telegram Gets an In-App Copilot Bot” reports:
Microsoft has added an official Copilot bot within the messaging app Telegram, which lets users search, ask questions, and converse with the AI chatbot. Copilot for Telegram is currently in beta but is free for Telegram users on mobile or desktop. People can chat with Copilot for Telegram like a regular conversation on the messaging app. Copilot for Telegram is an official Microsoft bot (make sure it’s the one with the checkmark and the username @CopilotOfficialBot).
You can “try it now.” Just navigate to Microsoft “Copilot for Telegram.” At this location, you can:
Meet your new everyday AI companion: Copilot, powered by GPT, now on Telegram. Engage in seamless conversations, access information, and enjoy a smarter chat experience, all within Telegram.
A dinobaby lecturer explains the Telegram APIs and its bot function for automating certain operations within the Telegram platform. Some in the class are looking at TikTok, scrolling Instagram, or reading about a breakthrough in counting large numbers of objects using a unique numerical recipe. But Telegram? WhatsApp and Signal are where the action is, right? Thanks, MSFT Copilot. You are into security and now Telegram. Keep your focus, please.
Next week, I will deliver a talk about Telegram and some related information about obfuscated messaging at the TechnoSecurity & Digital Forensics Conference. I no longer do too many lectures because I am an 80 year old dinobaby, and I hate flying and standing around talking to people 50 years younger than I. However, my team’s research into end-to-end encrypted messaging yielded some interesting findings. At the 2024 US National Cyber Crime Conference about 260 investigators listened to my 75 minute talk, and a number of them said, “We did not know that.” I will also do a Telegram-centric lecture at another US government event in September. But in this short post, I want to cover what the “deal” with Microsoft suggests.
Let’s get to it.
Telegram operates out of Dubai. The distributed team of engineers has been adding features and functions to what began as a messaging app in Russia. The “legend” of Telegram is an interesting story, but I remain skeptical about the company, its links with a certain country, and the direction in which the firm is headed. If you are not familiar with the service, it has morphed into a platform with numerous interesting capabilities. For some actors, Telegram can and has replaced the Dark Web with Telegram’s services. Note: Messages on Telegram are not encrypted by default as they are on some other E2EE messaging applications. Examples include contraband, “personal” services, and streaming video to thousands of people. Some Telegram users pay to get “special” programs. (Please, use your imagination.)
Why is Telegram undergoing this shift from humble messaging app to a platform? Our research suggests that there are three reasons. I want to point out that Pavel Durov does not have a public profile on the scale of a luminary like Elon Musk or Sam AI-Man, but he is out an about. He conducted an “exclusive” and possibly red-herring discussion with Tucker Carlson in April 2024. After the interview, Mr. Pavlov took direct action to block certain message flows from Ukraine into Russia. That may be one reason: Telegram is actively steering information about Ukraine’s view of Mr. Putin’s special operation. Yep, freedom.
Are there others? Let me highlight three:
- Mr. Pavlov and his brother who allegedly is like a person with two PhDs see an opportunity to make money. The Pavlovs, however, are not hurting for cash.
- American messaging apps have been fat and lazy. Mr. Pavlov is an innovator, and he wants to make darned sure that he rungs rings around Signal, WhatsApp, and a number of other outfits. Ego? My team thinks that is part of Mr. Pavlov’s motivation.
- Telegram is expanding because it may not be an independent, free-wheeling outfit. Several on my team think that Mr. Pavlov answers to a higher authority. Is that authority aligned with the US? Probably not.
Now the Microsoft deal?
Several questions may get you synapses in gear:
- Where are the data flowing through Telegram located / stored geographically? The service can regenerate some useful information for a user with a new device.
- Why tout freedom and free speech in April 2024 and several weeks later apply restrictions on data flow? Does this suggest a capability to monitor by user, by content type, and by other metadata?
- Why is Telegram exploring additional network enhancements? My team thinks that Mr. Pavlov has some innovations in obfuscation planned. If the company does implement certain technologies freely disclosed in US patents, what will that mean for analysts and investigators?
- Why a tie up with Microsoft? Whose idea was this? Who benefits from the metadata? What happens if Telegram has some clever ideas about smart software and the Telegram bot function?
Net net: Not too many people in Europe’s regulatory entities have paid much attention to Telegram. The entities of interest have been bigger fish. Now Telegram is growing faster than a Chernobyl boar stuffed on radioactive mushrooms. The EU is recalibrating for Telegram at this time. In the US, the “I did not know” reaction provides some insight into general knowledge about Telegram’s more interesting functions. Think pay-to-view streaming video about certain controversial subjects. Free storage and data transfer is provided by Telegram, a company which does not embrace the Netflix approach to entertainment. Telegram is, as I explain in my lectures, interesting, very interesting.
Stephen E Arnold, May 29, 2024
Facebook Scams: A Warning or a Tutorial?
May 27, 2024
 This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
This headline caught my attention: “Facebook Marketplace’s Dirty Dozen: The 15 Most Common Scams and How to Avoid Them.” I had hopes of learning about new, clever, wonderfully devious ways to commit fraud and other larcenous acts. Was I surprised? Here’s a list of the “15 most common scams.” I want to point out that there is scant (a nice way of saying “No back up data”) for the assertions. (I have a hunch that this “helpful” write up was assisted with some sort of software, possibly dumb software.) Let’s look at the list of the dozen’s 15 scams:
- Defective or counterfeit gadgets. Fix: Inspection required
- Bait-and-switch. Fix: Don’t engage in interaction
- Fake payment receipts. Fix: What? I don’t understand
- Mouth-watering giveaways. Fix: Ignore
- Overpayment by a buyer. Fix: What? I don’t understand
- Moving conversations out of Facebook. Fix: Don’t have them.
- Fake rental posting. Fix: Ignore
- Advance payment requests. Fix: Ignore
- Asking for confirmation codes. Fix: Ignore
- Asking for car deposits. Fix: Say, “No”
- Requesting unnecessary charges. Fix: Ignore
- Mailing items. Fix: Say, “No”
- Fake claims of lost packages. Fix: What?
- Counterfeit money. Fix: What?
- Clicking a link to fill out more information. Fix: Don’t
My concern with this list is that it does not protect the buyer. If anything, it provides a checklist of tactics for a would-be bad actor. The social engineering aspect of fraud is often more important than the tactic. In the “emotional” moment, a would-be buyer can fall for the most obvious scam; for example, trusting the seller because the request for a deposit seems reasonable or buying something else from the seller.
Trying to help? The customer or the scammer? You decide. Thanks, MSFT Copilot. Good cartoon. In your wheelhouse, is it?
What does one do to avoid Facebook scams? Here’s the answer:
Fraudsters can exploit you on online marketplaces if you’re not careful; it is easy not to be aware of a scam if you’re not as familiar. You can learn to spot common Facebook Marketplace scams to ensure you have a safe shopping experience. Remember that scams can happen between buyers and sellers, so always be wary of the transaction practices before committing. Otherwise, consider other methods like ordering from Amazon or becoming a third-party vendor on a trusted platform.
Yep, Amazon. On the other hand you can avoid scams by becoming a “third-party vendor on a trusted platform.” Really?
The problem with this write up is that the information mixes up what sellers do with what buyers do. Stepping back, why is Facebook singled out for this mish mash of scams and tactics. After all, in a face-to-face deal who pays with counterfeit cash? It is the buyer. Who is the victim? It is the seller. Who rents an apartment without looking at it? Answer: Someone in Manhattan. In other cities, alternatives to Facebook exist, and they are not available via Amazon as far as I know.
Facebook and other online vendors have to step up their game. The idea that the platform does not have responsibility to vet buyers and sellers is not something I find acceptable. Facebook seems pleased with its current operation. Perhaps it is time for more directed action to [a] address Facebook’s policies and [b] bring more rigor to write ups which seem to provide ideas for scammers in my opinion.
Stephen E Arnold, May 27, 2024
Legal Eagles Get Some Tail Feathers Plucked about BitTorrent
May 27, 2024
 This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
One Finnish law firm thinks it should be able to cut one party in out of the copyright enforcement process—the rightsholders themselves. The court disagrees. TorrentFreak reports, “Court Rejects Law Firm’s Bid to Directly Obtain BitTorrent Users’ Identities.” Writer Andy Maxwell explains:
“Requirements vary from region to region but when certain conditions are met, few courts deny genuine copyright holders the ability to enforce their rights under relevant law. One of the most fundamental requirements is that the entity making the claim has the necessary rights to do so. … In an application submitted to Finland’s Market Court on March 15, 2024, the law firm Hedman Partners Oy sought a court order to compel an unnamed internet service provider to provide the personal details of an unspecified number of subscribers. According to Hedman’s application, all are suspected of sharing copyrighted movies via BitTorrent, without first obtaining permission from two Danish rightsholders; Mis. Label ApS and Scanbox Entertainment A/S. Hedman Partners are well known for their work in the piracy settlement business in Scandinavia. The company fully understands the standards required before courts will issue a disclosure order. However, for reasons that aren’t made clear, the law firm would prefer to deal with these cases from a position of greater authority. This application appears to have served as the testing ground to determine whether that’s possible under Finland’s Copyright Act.”
The short answer: It is not possible. For the long, legalese-laced answer, see the article. Why did Hedman Partners try the move? Maxwell points out settlement efforts spearheaded by aggressive third-party legal teams tend to bring in more cash. Ah, there it is. A decision in favor of the firm would certainly not have benefitted the BitTorrent users, he notes. We may yet see whether that is correct—Hedman Partners has until June 18 to appeal the decision to the Supreme Court.
Will law enforcement step in?
Cynthia Murrell, May 27, 2024
Wanna Be Happy? Use the Internet
May 13, 2024
 This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
This essay is the work of a dinobaby. Unlike some folks, no smart software improved my native ineptness.
The glory days of the Internet have faded. Social media, AI-generated baloney, and brain numbing TikTok-esque short videos — Outstanding ways to be happy. What about endless online scams, phishing, and smishing, deep fake voices to grandma from grandchildren needing money — Yes, guaranteed uplifts to sagging spirits.
The idea of a payoff in a coffee shop is silly. Who would compromise academic standards for a latte and a pile of cash. Absolutely no one involved in academic pursuits. Good enough, MSFT Copilot. Good enough.
When I read two of the “real” news stories about how the Internet manufactures happiness, I asked myself, “Exactly what’s with this study?” The PR push to say happy things about online reminded me of the OII or Oxford Internet Institute and some of its other cheerleading. And what is the OII? It is an outfit which receives some university support, funds from private industry, and foundation cash; for example, the Shirley Institute.
In my opinion, it is often difficult to figure out if the “research” is wonky due to its methodology, the desire to keep some sources of funding writing checks, or a nifty way to influence policies in the UK and elsewhere. The magic of the “Oxford” brand gives the outfit some cachet for those who want to collect conference name tags to bedeck their office coat hangers.
The OII is back in the content marketing game. I read the BBC’s “Internet Access Linked to Higher Wellbeing, Study Finds” and the Guardian’s “Internet Use Is Associated with Greater Wellbeing, Global Study Finds.” Both articles are generated from the same PR-type verbiage. But the weirdness of the assertion is undermined by this statement from the BBC’s rewrite of the OII’s PR:
The study was not able to prove cause and effect, but the team found measures of life satisfaction were 8.5% higher for those who had internet access. Nor did the study look at the length of time people spent using the internet or what they used it for, while some factors that could explain associations may not have be considered.
The Oxford brand and the big numbers about a massive sample size cannot hide one awkward fact: There is little evidence that happiness drips from Internet use. Convenience? Yep. Entertainment? Yep. Crime? Yep. Self-harm, drug use or experimentation, meme amplification. Yep, yep, yep.
Several questions arise:
- Why is the message “online is good” suddenly big news? If anything, the idea runs counter to the significant efforts to contain access to potentially harmful online content in the UK and elsewhere. Gee, I wonder if the companies facing some type of sanctions are helping out the good old OII?
- What’s up with Oxford University itself? Doesn’t it have more substantive research to publicize? Perhaps Oxford should emulate the “Naked Scientist” podcast or lobby to get Melvin Bragg to report about more factual matters? Does Oxford have an identity crisis?
- And the BBC and the Guardian! Have the editors lost the plot? Don’t these professionals have first hand knowledge about the impact of online on children and young adults? Don’t they try to talk to their kids or grandkids at the dinner table when the youthful progeny of “real” news people are using their mobile phones?
I like facts which push back against received assumptions. But online is helping out those who use it needs a bit more precision, clearer thinking, and less tenuous cause-and-effect hoo-hah in my opinion.
Stephen E Arnold, May 13, 2024