FOGINT: Telegram Game Surfs on an Implied Link: Musk, X, Crypto Game
October 29, 2024
 Written by a humanoid dinobaby. No AI except the illustration.
Written by a humanoid dinobaby. No AI except the illustration.
The FOGINT team spotted a report from Decrypt.com. The article is “Why ‘X Empire’ Telegram Players Are Complaining to Elon Musk About the Airdrop.” If you don’t recognize the Crypto and Telegram jargon, the information in the Decrypt article will not make much sense.
For crypto folks, the X Empire Telegram game is news. According to the cited article:
Telegram tap-to-earn game X Empire will launch its X token on The Open Network (TON) on Thursday, but its reveal of airdrop allocations has drawn complaints from players who say they were deemed ineligible for a share of the rewards. And some of them are telling Elon Musk about it.
From the point of view of Telegram, X Empire is another entrepreneur leveraging the Telegram platform. With each popular egame, Telegram edges closer to its objective of becoming a very important player in what may be viewed as a Web3 service provider. In fact, when the potential payoff from its crypto interests, the craziness of some of the Group and Channel controversies becomes less important to the company. In fact, the hope for a Telegram initial public offering pay day is more important than refusing to cooperate with law enforcement. Telegram is working to appease France. Pavel Durov wants to get back to the 2024 and beyond opportunity with the Telegram crypto activities.
What is interesting to the FOGINT team are these considerations:
- Telegram’s bots and crypto linkages provide an interesting way to move funds and befuddle investigators
- Telegram has traction among crypto entities in Southeast Asia, and innovators operating without minimal regulatory oversight can use Telegram to extend their often illegal interests quickly and in a novel way
- Telegram’s bots or automated software embody a form of workflow automation which does not require getting involved with high profile, closely monitored organizations.
FOGINT wants to point out that Elon Musk is not involved in the X Empire play. However, Decrypt’s article suggests that some game players are complaining directly to him about the “earned” token policy. This is not a deep fake play. X Empire is an example of identity or entity surfing.
Investigators can make sense of some blockchain centric criminal activities. But the emergence of in game tokens, Telegram’s own STAR token, and their integration within the Telegram platform creates a one-stop shop for online crypto activities. Cyber investigators face another challenge: The non-US, largely unregulated Telegram operating as a virtual company with an address in Dubai. France took a bold step in detaining Pavel Durov. How will he adapt? It is unlikely he will be able to resist the lure of a big payoff from the innovations embodied in the Telegram platform.
Stephen E Arnold, October 29, 2024
AI Has An Invisible Language. Bad Actors Will Learn It
October 28, 2024
Do you remember those Magic Eyes back from the 1990s? You needed to cross your eyes a certain way to see the pony or the dolphin. The Magic Eyes were a phenomenon of early computer graphics and it was like an exclusive club with a secret language. There’s a new secret language on the Internet generated by AI and it could potentially sneak in malicious acts says Ars Technica: “Invisible Text That AI Chatbots Understand And Humans Can’t? Yep, It’s A Thing.”
The secret text could potentially include harmful instructions into AI chatbots and other code. The purpose would be to steal confidential information and conduct other scams all without a user’s knowledge:
“The invisible characters, the result of a quirk in the Unicode text encoding standard, create an ideal covert channel that can make it easier for attackers to conceal malicious payloads fed into an LLM. The hidden text can similarly obfuscate the exfiltration of passwords, financial information, or other secrets out of the same AI-powered bots. Because the hidden text can be combined with normal text, users can unwittingly paste it into prompts. The secret content can also be appended to visible text in chatbot output.”
The steganographic framework is built into a text encoding network and LLMs and read it. Researcher Johann Rehberger ran two proof-of-concept attacks with the hidden language to discover potential risks. He ran the tests on Microsoft 365 Copilot to find sensitive information. It worked:
“When found, the attacks induced Copilot to express the secrets in invisible characters and append them to a URL, along with instructions for the user to visit the link. Because the confidential information isn’t visible, the link appeared benign, so many users would see little reason not to click on it as instructed by Copilot. And with that, the invisible string of non-renderable characters covertly conveyed the secret messages inside to Rehberger’s server.”
What is nefarious is that the links and other content generated by the steganographic code is literally invisible. Rehberger and his team used a tool to decode the attack. Regular users are won’t detect the attacks. As we rely more on AI chatbots, it will be easier to infiltrate a person’s system.
Thankfully the Big Tech companies are aware of the problem, but not before it will probably devastate some people and companies.
Whitney Grace, October 28, 2024
FOGINT: FBI Nabs Alleged Crypto Swindlers
October 23, 2024
Nowhere does the phrase “buyer beware” apply more than the cryptocurrency market. But the FBI is on it. Crypto Briefing reports, “FBI Creates Crypto Token to Catch Fraudsters in Historic Market Manipulation Case.” The agency used its “NexFundAI” token to nab 18 entities—some individuals and also four major crypto firms: Gotbit, ZM Quant, CLS Global, and MyTrade. The mission was named “Operation Token Mirrors.” Snazzy. Writer Estefano Gomez explains:
“The charges stem from widespread fraud involving market manipulation and ‘wash trading’ designed to deceive investors and inflate crypto values. Working covertly, the FBI launched the token to attract the indicted firms’ services, which allegedly specialized in inflating trading volumes and prices for profit. The charges cover a broad scheme of wash trading, where defendants artificially inflated the value of more than 60 tokens, including the Saitama Token, which at its peak reached a market capitalization of $7.5 billion. The conspirators are alleged to have made false claims about the tokens and used deceptive tactics to mislead investors. After artificially pumping up the token prices, they would cash out at these inflated values, defrauding investors in a classic ‘pump and dump’ scheme. The crypto companies also allegedly hired market makers like ZM Quant and Gotbit to carry out these wash trades. These firms would execute sham trades using multiple wallets, concealing the true nature of the activity while creating fake trading volume to make the tokens seem more appealing to investors.”
If convicted, defendants could face up to two decades in prison. Several of those charged have already pled guilty. Authorities also shut down several trading bots used for wash trades and seized over $25 million in cryptocurrency. Assistant US Attorney Joshua Levy stresses that wash trading, long since illegal in traditional financial markets, is now also illegal in the crypto industry.
Cynthia Murrell, October 23, 2024
Pavel Durov and Telegram: In the Spotlight Again
October 21, 2024
 No smart software used for the write up. The art, however, is a different story.
No smart software used for the write up. The art, however, is a different story.
Several news sources reported that the entrepreneurial Pavel Durov, the found of Telegram, has found a way to grab headlines. Mr. Durov has been enjoying a respite in France, allegedly due to his contravention of what the French authorities views as a failure to cooperate with law enforcement. After his detainment, Mr. Durov signaled that he has cooperated and would continue to cooperate with investigators in certain matters.
A person under close scrutiny may find that the experience can be unnerving. The French are excellent intelligence operators. I wonder how Mr. Durov would hold up under the ministrations of Israeli and US investigators. Thanks, ChatGPT, you produced a usable cartoon with only one annoying suggestion unrelated to my prompt. Good enough.
Mr. Durov may have an opportunity to demonstrate his willingness to assist authorities in their investigation into documents published on the Telegram Messenger service. These documents, according to such sources as Business Insider and South China Morning Post, among others, report that the Telegram channel Middle East Spectator dumped information about Israel’s alleged plans to respond to Iran’s October 1, 2024, missile attack.
The South China Morning Post reported:
The channel for the Middle East Spectator, which describes itself as an “open-source news aggregator” independent of any government, said in a statement that it had “received, through an anonymous source on Telegram who refused to identify himself, two highly classified US intelligence documents, regarding preparations by the Zionist regime for an attack on the Islamic Republic of Iran”. The Middle East Spectator said in its posted statement that it could not verify the authenticity of the documents.
Let’s look outside this particular document issue. Telegram’s mostly moderation-free approach to the content posted, distributed, and pushed via the Telegram platform is like to come under more scrutiny. Some investigators in North America view Mr. Durov’s system as a less pressing issue than the content on other social media and messaging services.
This document matter may bring increased attention to Mr. Durov, his brother (allegedly with the intelligence of two PhDs), the 60 to 80 engineers maintaining the platform, and its burgeoning ancillary interests in crypto. Mr. Durov has some fancy dancing to do. One he is able to travel, he may find that additional actions will be considered to trim the wings of the Open Network Foundation, the newish TON Social service, and the “almost anything” goes approach to the content generated and disseminated by Telegram’s almost one billion users.
From a practical point of view, a failure to exercise judgment about what is allowed on Messenger may derail Telegram’s attempts to become more of a mover and shaker in the world of crypto currency. French actions toward Mr. Pavel should have alerted the wizardly innovator that governments can and will take action to protect their interests.
Now Mr. Durov is placing himself, his colleagues, and his platform under more scrutiny. Close scrutiny may reveal nothing out of the ordinary. On the other hand, when one pays close attention to a person or an organization, new and interesting facts may be identified. What happens then? Often something surprising.
Will Mr. Durov get that message?
Stephen E Arnold, October 21, 2024
Hey, France, Read Your Pavel-Grams: I Cooperate
October 18, 2024
 Just a humanoid processing information related to online services and information access.
Just a humanoid processing information related to online services and information access.
Did you know that Telegram has shared IPs since 2018. Do your homework!
Telegram is a favored message application, because it is supposed to protect user privacy, especially for crypto users. Not say, says Coin Telegraph in the article, “Telegram Has Been Disclosing User IPs Since 2018, Durov Says.” Before you start posting nasty comments about Telegram’s lies, the IPs the message is sharing belong to bad actors. CEO Pavel Durov shared on his Telegram channel that his company reports phone numbers and IP addresses to law enforcement.
The company has been disclosing criminal information to authorities since 2018, but only when proper legal procedure is followed. Telegram abides by formal legal requests when they are from relevant communication lines. Durov stressed that Telegram remains an anonymous centered app:
Durov said the news from last week showed that Telegram has been “streamlining and unifying its privacy policy across different countries.” He stressed that Telegram’s core principles haven’t changed, as the company has always sought to comply with relevant local laws ‘as long as they didn’t go against our values of freedom and privacy.’ He added: ‘Telegram was built to protect activists and ordinary people from corrupt governments and corporations — we do not allow criminals to abuse our platform or evade justice.”’
French authorities indicted Durov in August 2024 on six charges related to illicit activity via Telegram. He posted the $5.5 million bail in September, then revealed to the public how his company complies with legal requests after calling the charges misguided.
Kudos for Telegram disclosing the information to be transparent.
Whitney Grace, October 18, 2024
Deepfake Crime Surges With Scams
October 16, 2024
 Just a humanoid processing information related to online services and information access.
Just a humanoid processing information related to online services and information access.
Everyone with a brain knew that deepfakes, AI generated images, videos, and audio, would be used for crime. According to the Global Newswire, “Deepfake Fraud Doubles Down: 49% of Businesses Now Hit By Audio and Video Scams, Regula’s Survey Reveals.” Regula is a global developer of ID verification and forensic devices. The company released the survey: “The Deepfake Trends 2024” and it revealed some disturbing trends.
Regula’s survey discovered that there’s a 20% increase in deepfake videos from 2022. Meanwhile, fraud decision-makers across the globe reported a 49% increase encounter deepfakes and there’s also a 12% rise in fake audio. What’s even more interesting is that bad actors are still using old methods for identity fraud scams:
“As Regula’s survey shows, 58% of businesses globally have experienced identity fraud in the form of fake or modified documents. This happens to be the top identity fraud method for Mexico (70%), the UAE (66%), the US (59%), and Germany (59%). This implies that not only do businesses have to adapt their verification methods to deal with new threats, but they also are forced to combat old threats that continue to pose a significant challenge.”
Deepfakes will only get more advanced and worse. Bad actors and technology are like the illnesses: they evolve every season with new ways to make people sick while still delivering the common cold.
Whitney Grace, October 16, 2024
Flappy Bird Flutters to Life Thanks to the Power of the New Idol, Crypto
October 15, 2024
 Just a humanoid processing information related to online services and information access.
Just a humanoid processing information related to online services and information access.
Flappy Bird is coming out of retirement after a decade away. Launched in 2013, the original game was wildly popular and lucrative. However, less than a year later, its creator pulled it from app stores for being unintentionally addictive. Subsequently, players/addicts were willing to pay hundreds or thousands of dollars for devices that still had the game installed. Now it has reemerged as a Telegram crypto game. Much better. Decrypt reports, “What Is ‘Flappy Bird’ on Telegram? Iconic Game Returns with Crypto Twist.” Writer Ryan S. Gladwin tells us the game is basically the same as before, with a few additions just for crypto bros:
“Developed by the Flappy Bird Foundation, the Telegram game mixes in elements from other crypto games on the app, including the likes of Hamster Kombat, by allowing players to passively earn in-game points by obtaining upgrades. These are earned through a variety of ways, including watching ads and inviting friends.”
Naturally, a custom Flappy Bird token will be introduced. And, as with most of this year’s “tap-to-earn” games, it will reside on Telegram’s decentralized network, simply named The Open Network (TON). We learn:
"Yes, there will be a FLAP token launched in relation with the Telegram version of Flappy Bird. This has been confirmed in tweets from the official game account on Twitter (aka X), and the game will also offer staking rewards for the future token. Previously, The Flappy Bird Foundation said that it has plans to integrate The Open Network (TON)—the network that most tap-to-earn games launch tokens on. Notcoin, the tap-to-earn game that started the Telegram craze with the largest crypto gaming token launch of the year, is the ‘strategic publishing partner’ for Flappy Bird’s return. This partnership is set to help introduce The Open Network (TON) ecosystem to Flappy Bird with the game starting a ‘free mining event’ at launch called ‘Flap-a-TON.’ A mining event is usually a period of time in which players can make gameplay progress to get a cut of a future token airdrop.”
What a cutting-edge way to maximize engagement. If he was so upset about his game’s addictive qualities, why did creator Dong Nguyen sell it to an outfit that meant to crypto-tize it? In fact, he did not. After the game languished for four years, the trademark was deemed abandoned. A firm called Mobile Media Partners Inc. snapped up the languishing trademark and later sold it to one Gametech Holdings LLC, from whom the Flappy Bird Foundation bought it earlier this year. That must have been quite a surprise to the conscientious developer. Not only were Nguyen’s wishes for his game completely disregarded, he is receiving no compensation from the game’s reemergence. Classy.
Cynthia Murrell, October 15, 2024
FOGINT: UN Says Telegram Is a Dicey Outfit
October 14, 2024
 The only smart software involved in producing this short FOGINT post was Microsoft Copilot’s estimable art generation tool. Why? It is offered at no cost.
The only smart software involved in producing this short FOGINT post was Microsoft Copilot’s estimable art generation tool. Why? It is offered at no cost.
One of my colleagues forwarded a dump truck of links to articles about a UN Report. Before commenting on the report, I want to provide a snapshot of the crappy Web search tools and the useless “search” function on the UN Web site.
First, the title of the October 2024 report is:
Transnational Organized Crime and the Convergence of Cyber-Enabled Fraud, Underground Banking and Technological Innovation in Southeast Asia: A Shifting Threat Landscape
I want to point out that providing a full title in an online article is helpful to some dinobabies like me.
Second, including an explicit link to a document is also appreciated by some people, most of whom are over 25 years in age, of above average intelligence, and interested in online crime. With that in mind, here is the explicit link to the document:
https://www.unodc.org/roseap/uploads/documents/Publications/2024/TOC_Convergence_Report_2024.pdf
Now let’s look briefly at what the 142 page report says:
Telegram is a dicey outfit.
Not bad: 142 pages compressed to five words. Let look at two specifics and then I encourage you to read the full report and draw your own conclusions about the quite clever outfit Telegram.
The first passage which caught my attention was this one which is a list of the specialized software and services firms paying attention to Telegram. Here is that list. It is important because most of these outfits make their presence known to enforcement and intelligence entities, not the TikTok-type crowd:
Bitrace
Chainalysis
Chainargos
Chainvestigate
ChongLuaDao (Viet Nam)
Coeus
Crystal Intelligence
CyberArmor
Flare Systems
Flashpoint
Group-IB
Hensoldt Analytics
Intel 471
Kela
Magnet Forensics
Resecurity
Sophos
SlowMist
Trend Micro
TRM Labs
Other firms played ball with the UN, but these companies may have suggested, “Don’t tell anyone we assisted.” That’s my view; yours may differ.
The second interesting passage in the document for me was:
Southeast Asia faces unprecedented challenges posed by transnational organized crime and illicit economies. The region is witnessing a major convergence of different crime types and criminal services fueled by rapid and shifting advancements in physical, technological, and digital infrastructure have have allowed organized crime networks to expand these operations.
Cyber crime is the hot ticket in southeast Asia. I would suggest that the Russian oligarchs are likely to get a run for their money if these well-groomed financial wizards try to muscle in on what is a delightful mix of time Triads, sleek MBAs, and testosterone fueled crypto kiddies with motos, weapons and programming expertise. The mix of languages, laws, rules, and special purpose trade zones add some zest to the run-of-the-mill brushing activities. I will not suggest that many individuals who visit or live in Southeast Asia have a betting gene, but the idea is one worthy of Stuart Kauffman and his colleagues at the Santa Fe Institute. Gambling emerges from chaos and good old greed.
A third passage which I circled addressed Telegram. By the way, “Telegram” appears more than 100 times in the document. Here’s the snippet:
Providing further indication of criminal activity, Kokang casinos and associated companies have developed a robust presence across so-called ‘grey and black business’ Telegram channels facilitating cross-border ‘blockchain’ gambling, underground banking, money laundering, and related recruitment in Myanmar, Cambodia, China, and several other countries in East and Southeast Asia.
The key point to me is that this is a workflow process with a system and method spanning countries. The obvious problem is, “Whom does law enforcement arrest?” Another issue, “Where is the Telegram server?” The answer to the first question is, “In France.” The second question is more tricky and an issue that the report does not address. This is a problematic omission. The answer to the “Where is the Telegram server?” is, “In lots of places.” Telegram is into dApps or distributed applications. The servers outside of Moscow and St Petersburg are virtual. The providers or enablers of Telegram probably don’t know Telegram is a customer and have zero clue what’s going on in virtual machines running Telegram’s beefy infrastructure.
The report is worth reading. If you are curious about Telegram’s plumbing, please, write benkent2020 at yahoo dot com. The FOGINT team has a lecture about the components of the Telegram architecture as well as some related information about the company’s most recent social plays.
Stephen E Arnold, October 14, 2024
Cyber Criminals Rejoice: Quick Fraud Development Kit Announced
October 11, 2024
I am not sure the well-organized and managed OpenAI intended to make cyber criminals excited about their future prospects. Several Twitter enthusiasts pointed out that OpenAI makes it possible to develop an app in 30 seconds. Prashant posted:
App development is gonna change forever after today. OpenAI can build an iPhone app in 30 seconds with a single prompt. [emphasis added]
The expert demonstrating this programming capability was Romain Huet. The announcement of the capability débuted at OpenAI’s Dev Day.
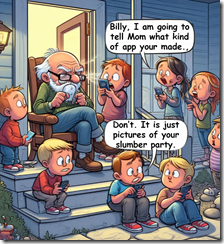
A clueless dinobaby is not sure what this group of youngsters is talking about. An app? Pictures of a slumber party? Thanks, MSFT Copilot, good enough.
What’s a single prompt mean? That’s not clear to me at the moment. Time is required to assemble the prompt, run it, check the outputs, and then fiddle with the prompt. Once the prompt is in hand, then it is easy to pop it into o1 and marvel at the 30 second output. Instead of coding, one prompts. Zip up that text file and sell it on Telegram. Make big bucks or little STARS and TONcoins. With some cartwheels, it is sort of money.
Is this quicker that other methods of cooking up an app; for example, some folks can do some snappy app development with Telegram’s BotFather service?
Let’s step back from the 30-second PR event.
Several observations are warranted.
First, programming certain types of software is becoming easier using smart software. That means that a bad actor may be able to craft a phishing play more quickly.
Second, specialized skills embedded in smart software open the door to scam automation. Scripts can generate other needed features of a scam. What once was a simple automated bogus email becomes an orchestrated series of actions.
Third, the increasing cross-model integration suggests that a bad actor will be able to add a video or audio delivering a personalized message. With some fiddling, a scam can use a phone call to a target and follow that up with an email. To cap off the scam, a machine-generated Zoom-type video call makes a case for the desired action.
The key point is that legitimate companies may want to have people they manage create a software application. However, is it possible that smart software vendors are injecting steroids into a market given little thought by most people? What is that market? I am thinking that bad actors are often among the earlier adopters of new, low cost, open source, powerful digital tools.
I like the gee whiz factor of the OpenAI announcement. But my enthusiasm is a fraction of that experienced by bad actors. Sometimes restraint and judgment may be more helpful than “wow, look at what we have created” show-and-tell presentations. Remember. I am a dinobaby and hopelessly out of step with modern notions of appropriateness. I like it that way.
Stephen E Arnold, October 11, 2024
What Can Cyber Criminals Learn from Automated Ad Systems?
October 10, 2024
 The only smart software involved in producing this short FOGINT post was Microsoft Copilot’s estimable art generation tool. Why? It is offered at no cost.
The only smart software involved in producing this short FOGINT post was Microsoft Copilot’s estimable art generation tool. Why? It is offered at no cost.
My personal opinion is that most online advertising is darned close to suspicious or outright legal behavior. “New,” “improved,” “Revolutionary” — Sure, I believe every online advertisement. But consider this: For hundreds of years those in the advertising business urged a bit of elasticity with reality. Sure, Duz does it. As a dinobaby, I assert that most people in advertising and marketing assume that reality and a product occupy different parts of a data space. Consequently most people — not just marketers, advertising executives, copywriters, and prompt engineers. I mean everyone.
An ad sales professional explains the benefits of Facebook, Google, and TikTok-type of sales. Instead of razor blades just sell ransomware as stolen credit cards. Thanks, MSFT Copilot. How are those security remediation projects with anti-malware vendors coming? Oh, sorry to hear that.
With a common mindset, I think it is helpful to consider the main points of “TikTok Joins the AI-Driven Advertising Pack to Compete with Meta for Ad Dollars.” The article makes clear that Google and Meta have automated the world of Madison Avenue. Not only is work mechanical, that work is informed by smart software. The implications for those who work the old fashioned way over long lunches and golf outings are that work methods themselves are changing.
The estimable TikTok is beavering away to replicate the smart ad systems of companies like the even more estimable Facebook and Google type companies. If TikTok is lucky as only an outfit linked with a powerful nation state can be, a bit of competition may find its way into the hardened black boxes of the digital replacement for Madison Avenue.
The write up says:
The pitch is all about simplicity and speed — no more weeks of guesswork and endless A/B testing, according to Adolfo Fernandez, TikTok’s director, global head of product strategy and operations, commerce. With TikTok’s AI already trained on what drives successful ad campaigns on the platform, advertisers can expect quick wins with less hassle, he added. The same goes for creative; Smart+ is linked to TikTok’s other AI tool, Symphony, designed to help marketers generate and refine ad concepts.
Okay, knowledge about who clicks what plus automation means less revenue for the existing automated ad system purveyors. The ideas are information about users, smart software, and automation to deliver “simplicity and speed.” Go fast, break things; namely, revenue streams flowing to Facebook and Google.
Why? Here’s a statement from the article answering the question:
TikTok’s worldwide ad revenue is expected to reach $22.32 billion by the end of the year, and increase 27.3% to $28.42 billion by the end of 2025, according to eMarketer’s March 2024 forecast. By comparison, Meta’s worldwide ad revenue is expected to total $154.16 billion by the end of this year, increasing 23.2% to $173.92 billion by the end of 2025, per eMarketer. “Automation is a key step for us as we enable advertisers to further invest in TikTok and achieve even greater return on investment,” David Kaufman, TikTok’s global head of monetization product and solutions, said during the TikTok.
I understand. Now let’s shift gears and ask, “What can bad actors learn from this seemingly routine report about jockeying among social media giants?”
Here are the lessons I think a person inclined to ignore laws and what’s left of the quaint notion of ethical behavior:
- These “smart” systems can be used to advertise bogus or non existent products to deliver ransomware, stealers, or other questionable software
- The mechanisms for automating phishing are simple enough for an art history or poli-sci major to use; therefore, a reasonably clever bad actor can whip up an automated phishing system without too much trouble. For those who need help, there are outfits like Telegram with its BotFather or helpful people advertising specialized skills on assorted Web forums and social media
- The reason to automate are simple: Better, faster, cheaper. Plus, with some useful data about a “market segment”, the malware can be tailored to hot buttons that are hard wired to a sucker’s nervous system.
- Users do click even when informed that some clicks mean a lost bank account or a stolen identity.
Is there a fix for articles which inform both those desperate to find a way to tell people in Toledo, Ohio, that you own a business selling aftermarket 22 inch wheels and alert bad actors to the wonders of automation and smart software? Nope. Isn’t online marketing a big win for everyone? And what if TikTok delivers a very subtle type of malware? Simple and efficient.
Stephen E Arnold, October 10, 2024