Preligens: An Important French AI Intelware Vendor May Be for Sale
April 3, 2024
 This essay is the work of a dumb dinobaby. No smart software required.
This essay is the work of a dumb dinobaby. No smart software required.
I profiled Preligens (formerly Earthcube), the French specialized software firm with quite remarkable smart software, in one of my lectures a couple of years ago. Preligens processes satellite imagery and uses its home-brew AI system to identify objects. When I was in Paris last year, I spoke with some of my former colleagues at Exalead (now a unit of Dassault Systèmes), acquaintances from my pre-retirement travels, and some individuals I met online. I picked up a couple of rumors. One was that Preligens had tuned its system to monitor the license tags and vehicle models of cars, busses, and trucks. When a vehicle made too many passes in front of a structure of interest, Preligens’ AI would note that event and send an alert. I am reluctant to include the screenshots of the capabilities of the Preligens’ system. When I presented information about the company at my law enforcement lectures, several people investigating big-money yachts asked for the company’s Web site. I could not provide a point of contact because one of Preligens’ sales professionals replied to me via email and then disappeared. Oh, well.
Thanks, MSFT Copilot. I asked for lights from the corner window. But no, MSFT knows best. So good enough.
Why am I mentioning a French outfit founded in 2016 when the buzz is emanating from Mistral, a hot AI startup?
One of the items of unsubstantiated information I picked up was that the company needed money, and it was for sale. I spotted “Preligens Announces Surrender And Issues Call For Bids For Acquisition” in one of my feeds. The write seemed to corroborate what I heard as rumor in Paris; namely, the company is for sale. The write up says in what appears to be machine-translated French:
…the founders of Preligens, Arnaud Guérin and Renaud Allioux, turned to Jean-Yves Courtois last year – appointing him president of the company – in the hope of turning things around….The echoes reports that Jean-Yves Courtois has launched a call for tenders from around twenty players for its takeover and hopes for tender submissions in mid-April. Thales and Safran also seem to have entered the race.
The challenge for Preligens is that the company is tightly bound to the French military and it is going to consummate a deal unless the buyer is an outfit which passes the scrutiny of the French bureaucracy. As one US government agency learned a couple of years ago, Preligens would not sell all or part of the company to a US buyer. The Franco-American kumbaya sounds good, but when it comes to high-value AI technology, the progress of the discussions moved like traffic around the Arc de Triomphe right after Bastille Day. (You absolutely must watch the Légion étrangère troop. Magnificent, slow, and a reminder that one does not fool around with dudes wearing aprons and kepis.)
A deal can be crafted, but it will take work. The Preligens’ AI system is outstanding and extensible to a number of intelware and policeware use cases. There are some videos on YouTube plus the firm’s Web site if you want more information. The military-oriented information is not on those public sources. If you see me at an appropriate conference, I may let you look through my presentation about identifying submarine pens in an area quite close to a US friendly nation. Oh, the submarine pen was previously unknown prior to Preligens’ smart software knitting together data from satellite imagery. That is impressive, but the system was able to estimate the size of the pen. Very cool.
Stephen E Arnold, April 3, 2024
US Bans Intellexa For Spying On Senator
March 22, 2024
 This essay is the work of a dumb dinobaby. No smart software required.
This essay is the work of a dumb dinobaby. No smart software required.
One of the worst ideas in modern society is to spy on the United States. The idea becomes worse when the target is a US politician. Intellexa is a notorious company that designs software to hack smartphones and transform them into surveillance devices. NBC News reports how Intellexa’s software was recently used in an attempt to hack a US senator: “US Bans Maker Of Spyware That Targeted A Senator’s Phone.”
Intellexa designed the software Predator that once downloaded onto a phone turns it into a surveillance device. Predator can turn on a phone’s camera and microphone, track a user’s location, and download files. The US Treasure Department banned Intellexa from conducting business in the US and US citizens are banned from working with the company. These are the most aggressive sanctions the US has ever taken against a spyware company.
The official ban also targets Intellexa’s founder Tan Dilian, employee Sara Hamou, and four companies that are affiliated with it. Predator is also used by authoritarian governments to spy on journalists, human rights workers, and anyone deemed “suspicious:”
“An Amnesty International investigation found that Predator has been used to target journalists, human rights workers and some high-level political figures, including European Parliament President Roberta Metsola and Taiwan’s outgoing president, Tsai Ing-Wen. The report found that Predator was also deployed against at least two sitting members of Congress, Rep. Michael McCaul, R-Texas, and Sen. John Hoeven, R-N.D.”
John Scott-Railton is a senior spyware researcher at the University of Toronto’s Citizen Lab and he said the US Treasury’s sanctions will rock the spyware world. He added it could also inspire people to change their careers and leave countries.
Predator isn’t the only company that makes spyware. Hackers can also design their own then share it with other bad actors.
Whitney Grace, March 22, 2024
NSO Group: Pegasus Code Wings Its Way to Meta and Mr. Zuckerberg
March 7, 2024
 This essay is the work of a dumb dinobaby. No smart software required.
This essay is the work of a dumb dinobaby. No smart software required.
NSO Group’s senior managers and legal eagles will have an opportunity to become familiar with an okay Brazilian restaurant and a waffle shop. That lovable leader of Facebook, Instagram, Threads, and WhatsApp may have put a stick in the now-ageing digital bicycle doing business as NSO Group. The company’s mark is pegasus, which is a flying horse. Pegasus’s dad was Poseidon, and his mom was the knock out Gorgon Medusa, who did some innovative hair treatments. The mythical pegasus helped out other gods until Zeus stepped in an acted with extreme prejudice. Quite a myth.
Poseidon decides to kill the mythical Pegasus, not for its software, but for its getting out of bounds. Thanks, MSFT Copilot. Close enough.
Life imitates myth. “Court Orders Maker of Pegasus Spyware to Hand Over Code to WhatsApp” reports that the hand over decision:
is a major legal victory for WhatsApp, the Meta-owned communication app which has been embroiled in a lawsuit against NSO since 2019, when it alleged that the Israeli company’s spyware had been used against 1,400 WhatsApp users over a two-week period. NSO’s Pegasus code, and code for other surveillance products it sells, is seen as a closely and highly sought state secret. NSO is closely regulated by the Israeli ministry of defense, which must review and approve the sale of all licenses to foreign governments.
NSO Group hired former DHS and NSA official Stewart Baker to fix up NSO Group gyro compass. Mr. Baker, who is a podcaster and affiliated with the law firm Steptoe and Johnson. For more color about Mr. Baker, please scan “Former DHS/NSA Official Stewart Baker Decides He Can Help NSO Group Turn A Profit.”
A decade ago, Israel’s senior officials might have been able to prevent a social media company from getting a copy of the Pegasus source code. Not anymore. Israel’s home-grown intelware technology simply did not thwart, prevent, or warn about the Hamas attack in the autumn of 2023. If NSO Group were battling in court with Harris Corp., Textron, or Harris Corp., I would not worry. Mr. Zuckerberg’s companies are not directly involved with national security technology. From what I have heard at conferences, Mr. Zuckerberg’s commercial enterprises are responsive to law enforcement requests when a bad actor uses Facebook for an allegedly illegal activity. But Mr. Zuckerberg’s managers are really busy with higher priority tasks. Some folks engaged in investigations of serious crimes must be patient. Presumably the investigators can pass their time scrolling through #Shorts. If the Guardian’s article is accurate, now those Facebook employees can learn how Pegasus works. Will any of those learnings stick? One hopes not.
Several observations:
- Companies which make specialized software guard their systems and methods carefully. Well, that used to be true.
- The reorganization of NSO Group has not lowered the firm’s public relations profile. NSO Group can make headlines, which may not be desirable for those engaged in national security.
- Disclosure of the specific Pegasus systems and methods will get a warm, enthusiastic reception from those who exchange ideas for malware and related tools on private Telegram channels, Dark Web discussion groups, or via one of the “stealth” communication services which pop up like mushrooms after rain in rural Kentucky.
Will the software Pegasus be terminated? I remain concerned that source code revealing how to perform certain tasks may lead to downstream, unintended consequences. Specialized software companies try to operate with maximum security. Now Pegasus may be flying away unless another legal action prevents this.
Where is Zeus when one needs him?
Stephen E Arnold, March 7, 2024
The NSO Group Back in the News: Is That a Good Thing?
January 24, 2024
 This essay is the work of a dumb dinobaby. No smart software required.
This essay is the work of a dumb dinobaby. No smart software required.
Some outfits struggle to get PR, not the NSO Group. The situation is no “dream.” I spotted this write up in 9 to 5 Mac: “Apple Wins Early Battle against NSO after Suing Spyware Mercenaries for Attacking iPhone Users.” For me, the main point of the article is:
Judge Donato ruled that NSO Group’s request for dismissal in the US in favor of a trial in Israel didn’t meet the bar. Instead, Judge Donato suggested that Apple would face the same challenges in Israel that NSO faces in the US.
A senior manager who is an attorney skilled in government processes looks at the desk in his new office. Wow, that looks untidy. Thanks, MSFT Copilot Bing thing. How’s that email security issue coming along? Ah, good enough, you say?
I think this means that the legal spat will be fought in the US of A. Here’s the sentence quoted by 9 to 5 Mac which allegedly appeared in a court document:
NSO has not demonstrated otherwise. NSO also overlooks the fact that the challenges will be amenable to a number of mitigating practices.
The write up includes this passage:
An Apple spokesperson tells 9to5Mac that the company will continue to protect users against 21st century mercenaries like the NSO Group. Litigation against the Pegasus spyware maker is part of a larger effort to protect users…
From my point of view, the techno feudal outfit has surfed on the PR magnetism of the NSO Group. Furthermore, the management team at NSO Group faces what seems to be a bit of a legal hassle. Some may believe that the often ineffective Israeli cyber security technology which failed to signal, thwart, or disrupt the October 2023 dust up requires more intense scrutiny. NSO Group, therefore, is in the spotlight.
More interesting from my vantage point is the question, “How can NSO Group’s lawyering-savvy senior management not demonstrate its case in such a way to, in effect, kill some of the PR magnetism. Take it from me. This is not a “dream” assignment for NSO Group’s legal eagles. I would also be remiss if I did not mention that Apple has quite a bit of spare cash with which to feather the nest of legal eagles. Apple wants to be perceived as the user’s privacy advocate and BFF. When it comes to spending money and rounding up those who love their Apple devices, the estimable Cupertino outfit may be a bit of a challenge, even to attorneys with NSA and DHS experience.
As someone said about publicity, any publicity is good publicity. I am not sure the categorical affirmative is shared by everyone involved with NSO Group. And where is Hulio? He’s down by the school yard. He doesn’t know where he’s going, but Hulio is going the other way. (A tip of the hat to Paul Simon and his 1972 hit.)
Stephen E Arnold, January 24, 2024
Pegasus Equipped with Wings Stomps Around and Leaves Hoof Prints
January 8, 2024
 This essay is the work of a dumb dinobaby. No smart software required.
This essay is the work of a dumb dinobaby. No smart software required.
The NSO Group’s infamous Pegasus spyware is in the news again, this time in India. Newsclick reveals, “New Forensic Report Finds ‘Damning Revelations’ of ‘Repeated’ Pegasus Use to Target Indian Scribes.” The report is a joint project by Amnesty International and The Washington Post. It was spurred by two indicators. First, routine monitoring exercise in June 2023 turned up traces of Pegasus on certain iPhones. Then, in October, several journalists and Opposition party politicians received Apple alerts warning of “State-sponsored attackers.” The article tells us:
“‘As a result, Amnesty International’s Security Lab undertook a forensic analysis on the phones of individuals around the world who received these notifications, including Siddharth Varadarajan and Anand Mangnale. It found traces of Pegasus spyware activity on devices owned by both Indian journalists. The Security Lab recovered evidence from Anand Mangnale’s device of a zero-click exploit which was sent to his phone over iMessage on 23 August 2023, and designed to covertly install the Pegasus spyware. … According to the report, the ‘attempted targeting of Anand Mangnale’s phone happened at a time when he was working on a story about an alleged stock manipulation by a large multinational conglomerate in India.’”
This was not a first for The Wire co-founder Siddharth Varadarajan. His phone was also infected with Pegasus back in 2018, according to forensic analysis ordered by the Supreme Court of India. The latest findings have Amnesty International urging bans on invasive, opaque spyware worldwide. Naturally, The NSO Group continues to insist all its clients are “vetted law enforcement and intelligence agencies that license our technologies for the sole purpose of fighting terror and major crime” and that it has policies in place to prevent “targeting journalists, lawyers and human rights defenders or political dissidents that are not involved in terror or serious crimes.” Sure.
Meanwhile, some leaders of India’s ruling party blame Apple for those security alerts, alleging the “company’s internal threat algorithms were faulty.” Interesting deflection. We’re told an Apple security rep was called in and directed to craft some other, less alarming explanation for the warnings. Is this because the government itself is behind the spyware? Unclear; Parliament refuses to look into the matter, claiming it is sub judice. How convenient.
Cynthia Murrell, January 8, 2024
Lawyer, Former Government Official, and Podcaster to Head NSO Group
January 2, 2024
 This essay is the work of a dumb dinobaby. No smart software required.
This essay is the work of a dumb dinobaby. No smart software required.
The high-profile intelware and policeware vendor NSO Group has made clear that specialized software is a potent policing tool. NSO Group continues to market its products and services at low-profile trade shows like those sponsored by an obscure outfit in northern Virginia. Now the firm has found a new friend in a former US official. TechDirt reports, “Former DHS/NSA Official Stewart Baker Decides He Can Help NSO Group Turn a Profit.” Writer Tim Cushing tells us:
“This recent filing with the House of Representatives makes it official: Baker, along with his employer Steptoe and Johnson, will now be seeking to advance the interests of an Israeli company linked to abusive surveillance all over the world. In it, Stewart Baker is listed as the primary lobbyist. This is the same Stewart Baker who responded to the Commerce Department blacklist of NSO by saying it wouldn’t matter because authoritarians could always buy spyware from… say…. China.”
So, the reasoning goes, why not allow a Western company to fill that niche? This perspective apparently makes Baker just the fellow to help NSO buff up NSO Group’s reputation. Cushing predicts:
“The better Baker does clearing NSO’s tarnished name, the sooner it and its competitors can return to doing the things that got them in trouble in the first place. Once NSO is considered somewhat acceptable, it can go back to doing the things that made it the most money: i.e., hawking powerful phone exploits to human rights abusers. But this time, NSO has a former US government official in its back pocket. And not just any former government official but one who spent months telling US citizens who were horrified by the implications of the Snowden leaks that they were wrong for being alarmed about bulk surveillance.”
Perhaps the winning combination for the NSO Group is a lawyer, former US government official, and a podcaster in one sleek package will do the job? But there are now alternatives to the Pegasus solution. Some of these do not have the baggage carted around by the stealthy flying horse.
Perhaps there will be a podcast about NSO Group in the near future.
Cynthia Murrell, January 2, 2024
Missing Signals: Are the Tools or Analysts at Fault?
November 7, 2023
 This essay is the work of a dumb humanoid. No smart software required.
This essay is the work of a dumb humanoid. No smart software required.
Returning from a trip to DC yesterday, I thought about “signals.” The pilot — a specialist in hit-the-runway-hard landings — used the word “signals” in his welcome-aboard speech. The word sparked two examples of missing signals. The first is the troubling kinetic activities in the Middle East. The second is the US Army reservist who went on a shooting rampage.
The intelligence analyst says, “I have tools. I have data. I have real time information. I have so many signals. Now which ones are important, accurate, and actionable?” Our intrepid professionals displays the reality of separating the signal from the noise. Scary, right? Time for a Starbuck’s visit.
I know zero about what software and tools, systems and informers, and analytics and smart software the intelligence operators in Israel relied upon. I know even less about what mechanisms were in place when Robert Card killed more than a dozen people.
The Center for Strategic and International Studies published “Experts React: Assessing the Israeli Intelligence and Potential Policy Failure.” The write up stated:
It is incredible that Hamas planned, procured, and financed the attacks of October 7, likely over the course of at least two years, without being detected by Israeli intelligence. The fact that it appears to have done so without U.S. detection is nothing short of astonishing. The attack was complex and expensive.
And one more passage:
The fact that Israeli intelligence, as well as the international intelligence community (specifically the Five Eyes intelligence-sharing network), missed millions of dollars’ worth of procurement, planning, and preparation activities by a known terrorist entity is extremely troubling.
Now let’s shift to the Lewiston Maine shooting. I had saved on my laptop “Six Missed Warning Signs Before the Maine Mass Shooting Explained.” The UK newspaper The Guardian reported:
The information about why, despite the glaring sequence of warning signs that should have prevented him from being able to possess a gun, he was still able to own over a dozen firearms, remains cloudy.
Those “signs” included punching a fellow officer in the US Army Reserve force, spending some time in a mental health facility, family members’ emitting “watch this fellow” statements, vibes about issues from his workplace, and the weapon activity.
On one hand, Israel had intelligence inputs from just about every imaginable high-value source from people and software. On the other hand, in a small town the only signal that was not emitted by Mr. Card was buying a billboard and posting a message saying, “Do not invite Mr. Card to a church social.”
As the plane droned at 1973 speeds toward the flyover state of Kentucky, I jotted down several thoughts. Like or not, here these ruminations are:
- Despite the baloney about identifying signals and determining which are important and which are not, existing systems and methods failed bigly. The proof? Dead people. Subsequent floundering.
- The mechanisms in place to deliver on point, significant information do not work. Perhaps it is the hustle bustle of everyday life? Perhaps it is that humans are not very good at figuring out what’s important and what’s unimportant. The proof? Dead people. Constant news releases about the next big thing in open source intelligence analysis. Get real. This stuff failed at the scale of SBF’s machinations.
- The uninformed pontifications of cyber security marketers, the bureaucratic chatter flowing from assorted government agencies, and the cloud of unknowing when the signals are as subtle as the foghorn on cruise ship with a passenger overboard. Hello, hello, the basic analysis processes don’t work. A WeWork investor’s thought processes were more on point than the output of reporting systems in use in Maine and Israel.
After the aircraft did the thump-and-bump landing, I was able to walk away. That’s more than I can say for the victims of analysis, investigation, and information processing methods in use where moose roam free and where intelware is crafted and sold like canned beans at TraderJoe’s.
Less baloney and more awareness that talking about advanced information methods is a heck of a lot easier than delivering actual signal analysis.
Stephen E Arnold, November 7, 2023
test
Video Analysis: Do Some Advanced Systems Have Better Marketing Than Technology?
October 16, 2023
![Vea4_thumb_thumb_thumb_thumb_thumb_t[2] Vea4_thumb_thumb_thumb_thumb_thumb_t[2]](https://arnoldit.com/wordpress/wp-content/uploads/2023/10/Vea4_thumb_thumb_thumb_thumb_thumb_t2_thumb-20.gif) Note: This essay is the work of a real and still-alive dinobaby. No smart software involved, just a dumb humanoid.
Note: This essay is the work of a real and still-alive dinobaby. No smart software involved, just a dumb humanoid.
I am tempted to list some of the policeware and intelware companies which tout video analysis capabilities. If we narrow our focus to Israel, there are a number of companies which offer software and systems that can make sense of video data. Years ago, I attended a briefing and the company (which I will not name) showed that its system could zip through a 90 minute video of a soccer (football) match and identify the fouls and the goals. Like most demonstrations, the system worked perfectly. In actual real world situations, the system did not work. Video footage is a problem, but there are companies which assert their developers’ confection.
Aggressive bunnies get through the farmer’s fence. The smart surveillance cameras emit a faint beep. The bunnies are having a great time. The farmer? Not so much. Thank you, MidJourney. You do a nice bunny.
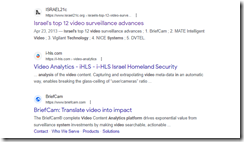
Here’s the results of the query “video analysis Israel.” Notice that I am not including the name of a company nor a specific country. Google returned ads and video thumbnails and this result:
The cited article is from Israel21c 2013 write up “Israel’s Top 12 Video Surveillance Advances.” The cited article reports as actual factual:
Combing such vast amounts of material [from the Boston Marathon bombing in 2013] would have taken months, or even years in the past, but with new video analytics technologies developed by Israel’s BriefCam, according to the publication IsraelDefense, it took authorities just a few days to identify and track Tamerlan and Dzhokhar Tsarneav, the two main suspects in the attack which killed three, and wounded 183. Within five days one of the terrorists was dead, the other arrested after a 22-hour manhunt.
BriefCam is now owned by Canon, the Japanese camera maker. Imagine the technical advances in the last 10 years.
I don’t know if Israel had a BriefCam system at its disposal in the last six months. My understanding is that the Israel Defense Force and related entities have facial recognition systems. These can work on still pictures as well as digital video.
Why is this important?
The information in the San Francisco Chronicle article “Hamas Practiced in Plain Sight, Posting Video of Mock Attack Weeks Before Border Breach” asserts:
A slickly produced two-minute propaganda video posted to social media by Hamas on Sept. 12 shows fighters using explosives to blast through a replica of the border gate, sweep in on pickup trucks and then move building by building through a full-scale reconstruction of an Israeli town, firing automatic weapons at human-silhouetted paper targets. The Islamic militant group’s live-fire exercise dubbed operation “Strong Pillar” also had militants in body armor and combat fatigues carrying out operations that included the destruction of mock-ups of the wall’s concrete towers and a communications antenna, just as they would do for real in the deadly attack last Saturday.
If social media monitoring systems worked, the video should have been flagged and routed to the IDF. If the video analysis and facial recognition systems worked, an alert to a human analyst could have sparked a closer look. It appears that neither of these software-intermediated actions took place and found their way to a human analyst skilled in figuring out what the message payload of the video was. Who found the video? Based on the tag line to the cited article, the information was located by reporters for the Associated Press.
What magical research powers did the AP have? None as it turns out. The article reports:
The Associated Press reviewed more than 100 videos Hamas released over the last year, primarily through the social media app Telegram. Using satellite imagery, the AP was able to verify key details, as well as identify five sites Hamas used to practice shooting and blowing holes in Israel’s border defenses. The AP matched the location of the mocked-up settlement from the Sept 12 video to a patch of desert outside Al-Mawasi, a Palestinian town on the southern coast of the Gaza Strip. A large sign in Hebrew and Arabic at the gate says “Horesh Yaron,” the name of a controversial Israeli settlement in the occupied Palestinian West Bank.
I don’t want to be overly critical of tools like BriefCam or any other company. I do want to offer several observations from my underground office in rural Kentucky:
- The Hamas attack was discernable via humans who were paying attention. Were people in the IDF and related agencies paying attention? Apparently something threw a wrench in a highly-visible, aggressively marketed intelligence capability, right?
- What about home grown video and facial recognition systems? Yes, what about them. My hunch is that the marketing collateral asserts some impressive capabilities. What is tough to overlook is that for whatever reason (human or digital), the bunny got through the fence and did damage to some precious, fragile organic material.
- Are other policeware and intelware vendors putting emphasis on marketing instead of technical capabilities? My experience over the last half century says, “When sales slow down and the competition heats up, marketing takes precedence over the actual product.”
Net net: Is it time for certification of cyber security technology? Is it time for an external audit of intelligence operations? The answer to both questions, I think, is, “Are you crazy?”
Stephen E Arnold, October 16, 2023
xx
xx
xx
Intelware: Some Advanced Technology Is Not So New
October 11, 2023
![Vea4_thumb_thumb_thumb_thumb_thumb_t[2] Vea4_thumb_thumb_thumb_thumb_thumb_t[2]](https://arnoldit.com/wordpress/wp-content/uploads/2023/10/Vea4_thumb_thumb_thumb_thumb_thumb_t2_thumb-8.gif) Note: This essay is the work of a real and still-alive dinobaby. No smart software involved, just a dumb humanoid.
Note: This essay is the work of a real and still-alive dinobaby. No smart software involved, just a dumb humanoid.
I read “European Spyware Consortium Supplied Despots and Dictators.” The article is a “report” about intelware vendors. The article in Spiegel International is a “can you believe this” write up. The article identifies a number of companies past and present. Plus individuals are identified.
The hook is technology that facilitates exfiltration of data from mobile devices. Mobile phones are a fashion item and a must have for many people. It does not take much insight to conclude that data on these ubiquitous gizmos can provide potentially high value information. Even better, putting a software module on a mobile device of a person of interest can save time and expense. Modern intelligence gathering techniques are little more than using technology to minimize the need for humans sitting in automobiles or technicians planting listening devices in interesting locations. The other benefits of technology include real time or near real time data acquisition, geo-location data, access to the digital information about callers and email pals, and data available to the mobile’s ever improving cameras and microphones.
The write up points out:
One message, one link, one click. That’s all it takes to lose control of your digital life, unwittingly and in a matter of seconds.
The write up is story focused, probably because a podcast or a streaming video documentary was in the back of the mind of the writers and possibly Spiegel International itself. If you like write ups that have a slant, you will find the cited article interesting.
I want to mentions several facets of the write up which get less attention from “real” journalists.
First, the story of the intelware dates back to the late 1970s. Obviously some of the technology has been around for decades, although refined over time. If this “shady” technology were a problem, why has it persisted, been refined, and pressed into service around the world by many countries? It is tempting to focus on a current activity because it makes a good story, but the context and longevity of some of the systems and methods are interesting to me. But 40 years?
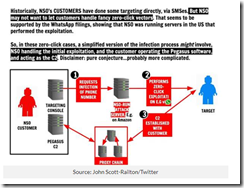
Second, in the late 1970s and the block diagrams I have seen presenting the main features of the Amesys system (i2e Technologies) and its direct descendants have had remarkable robustness. In fact, were one to look at the block diagram for a system provided to a controversial government in North Africa and one of the NSO Group Pegasus block diagrams, the basics are retained. Why? A good engineering solution is useful even thought certain facets of the system are improved with modern technology. What’s this mean? From my point of view, the clever individual or group eager to replicate this type of stealth intelware can do it, just with modern tools and today’s robust cloud environment. The cloud was not a “thing” in 1980, but today it is a Teflon for intelware. This means quicker, faster, better, cheaper, and smarter with each iteration.
Source: IT News in Australia
Third, this particular type of intelware is available from specialized software companies worldwide. Want to buy a version from a developer in Spain? No problem. How about a Chinese variety? Cultivate your contacts in Hong Kong or Singapore and your wish will be granted. What about a version from an firm based in India? No problem, just hang out at telecommunications conference in Mumbai.
Net net: Newer and even more stealthy intelware technologies are available today. Will these be described and stories about the use of them be written? Yep. Will I identify some of these firms? Sure, just attend one of my lectures for law enforcement and intelligence professionals. But the big question is never answered, “Why are these technologies demonstrating such remarkable magnetic appeal?” And a related question, “Why do governments permit these firms to operate?”
Come on, Spiegel International. Write about a more timely approach, not one that is decades old and documented in detail on publicly accessible sources. Oh, is location tracking enabled on your phone to obviate some of the value of Signal, Telegram, and Threema encrypted messaging apps?
PS. Now no clicks are needed. The technology can be deployed when a mobile number is known and connected to a network. There is an exception too. The requisite code can be pre-installed on one’s mobile device. Is that a story? Nah, that cannot be true. I agree.
Stephen E Arnold, October 11, 2023
Israeli Intelware: Is It Time to Question Its Value?
October 9, 2023
![Vea4_thumb_thumb_thumb_thumb_thumb_t[2] Vea4_thumb_thumb_thumb_thumb_thumb_t[2]](https://arnoldit.com/wordpress/wp-content/uploads/2023/10/Vea4_thumb_thumb_thumb_thumb_thumb_t2_thumb-2.gif) Note: This essay is the work of a real and still-alive dinobaby. No smart software involved, just a dumb humanoid.
Note: This essay is the work of a real and still-alive dinobaby. No smart software involved, just a dumb humanoid.
In 2013, I believe that was the year, I attended an ISS TeleStrategies Conference. A friend of mine wanted me to see his presentation, and I was able to pass the Scylla and Charybdis-inspired security process and listen to the talk. (Last week I referenced that talk and quoted a statement posted on a slide for everyone in attendance to view. Yep, a quote from 2013, maybe earlier.)
After the talk, I walked quickly through the ISS exhibit hall. I won’t name the firms exhibiting because some of these are history (failures), some are super stealthy, and others have been purchased by other outfits as the intelware roll ups continue. I do recall a large number of intelware companies with their headquarters in or near Tel Aviv, Israel. My impression, as I recall, was that Israel’s butt-kicking software could make sense of social media posts, Dark Web forum activity, Facebook craziness, and Twitter disinformation. These Israeli outfits were then the alpha vendors. Now? Well, maybe a bit less alpha drifting to beta or gamma.
One major to another: “Do you think our intel was wrong?” The other officer says, “I sat in a briefing teaching me that our smart software analyzed social media in real time. We cannot be surprised. We have the super duper intelware.” The major says, jarred by an explosion, “Looks like we were snookered by some Madison Avenue double talk. Let’s take cover.” Thanks, MidJourney. You do understand going down in flames. Is that because you are thinking about your future?
My impression was that the Israeli-developed software shared a number of functional and visual similarities. I asked people at the conference if they had noticed the dark themes, the similar if not identical timeline functions, and the fondness for maps on which data were plotted and projected. “Peas in a pod,” my friend, a former NATO officer told me. Are not peas alike?
The reason — and no one has really provided this information — is that the developers shared a foxhole. The government entities in Israel train people with the software and systems proven over the years to be useful. The young trainees carry their learnings forward in their career. Then when mustered out, a few bright sparks form companies or join intelware giants like Verint and continue to enhance existing tools or building new ones. The idea is that life in the foxhole imbues those who experience it with certain similar mental furniture. The ideas, myths, and software experiences form the muddy floor and dirt walls of the foxhole. I suppose one could call this “digital bias”, which later manifests itself in the dozens of Tel Aviv -based intelware, policeware, and spyware companies’ products and services.
Why am I mentioning this?
The reason is that I was shocked and troubled by the allegedly surprise attack. If you want to follow the activity, navigate to X.com and search that somewhat crippled system for #OSINT. Skip top and go to the “Latest” tab.
Several observations:
- Are the Israeli intelware products (many of which are controversial and expensive) flawed? Obviously excellent software processing “signals” was blind to the surprise attack, right?
- Are the Israeli professionals operating the software unable to use it to prevent surprise attacks? Obviously excellent software in the hands of well-trained professionals flags signals and allows action to be taken when warranted. Did that happen? Has Israeli intel training fallen short of its goal of protecting the nation? Hmmm. Maybe, yes.
- Have those who hype intelware and the excellence of a particular system and method been fooled, falling into the dark pit of OSINT blind spots like groupthink and “reasoning from anecdote, not fact”? I am leaning toward a “yes”, gentle reader.
The time for a critical look at what works and what doesn’t is what the British call “from this day” work. The years of marketing craziness is one thing, but when either the system or the method allows people to be killed without warning or cause broadcasts one message: “Folks, something is very, very wrong.”
Perhaps certification of these widely used systems is needed? Perhaps a hearing in an appropriate venue is warranted?
Blind spots can cause harm. Marketers can cause harm. Poorly trained operators can cause harm. Even foxholes require tidying up. Technology for intelligence applications is easy to talk about, but it is now clear to everyone engaged in making sense of signals, one country’s glamped up systems missed the wicket.
Stephen E Arnold, October 9, 2023