Three Constants: Death, Taxes, and NSO?
December 8, 2022
I know the special action is interesting to some. Plus, there’s a volcanic eruption outputting. And there is the Twitter saga, the NGX drama, and exciting World Cup. (Did Spain lose to Japan to avoid Seleção Brasileira? Of course not.)
But poking through the PR fumes and rising near the flocks of legal eagles circling for prey is the NSO Group. Navigate to “Why We’re Suing NSO Group.” You will learn that El Faro, a real news outfit in the pace-setting Republic of Salvador, and its taking action against NSO Group. The company has become the touchstone for allegedly unlawful surveillance of individuals.
The write up asserts:
Beginning in June 2020, at least 22 people associated with El Faro were the targets of spyware attacks. Over a period of about 18 months, their iPhones were accessed remotely and surreptitiously, their communications and activities monitored, and their personal data stolen. Many of these attacks occurred when the journalists were communicating with confidential sources, and reporting on abuses by the Salvadoran government.
The legal action is described this way:
the Knight Institute filed suit against NSO Group on behalf of 15 of the El Faro employees whose iPhones were infected with Pegasus spyware….Our complaint explains that NSO Group’s development and deployment of the spyware violated, among other laws, the Computer Fraud and Abuse Act, which prohibits accessing computers without authorization. We argue that our case belongs in a U.S. court because the spyware attacks violated U.S. law, because they were intended to deter journalism that is important to hundreds of thousands of American readers, and because NSO Group’s development and deployment of Pegasus involved deliberate and sustained attacks on the U.S. infrastructure of U.S. technology companies—including Apple, which itself sued NSO Group last year, contending that the spyware manufacturer had damaged its business and harmed its users.
Death, taxes, and NSO—Are these three constants of modern life?
Stephen E Arnold, December 8, 2022
Google and Crypto: Solana Should Anyone Ask
November 18, 2022
I read “Google Cloud Just Became a Solana Validator.” The article explains what Google has chosen to reveal to those who follow the company via “real” journalists; namely:
Google’s cloud computing division Google Cloud announced on Saturday that it’s now running a validator on the Solana blockchain, and will soon add features aimed at welcoming Solana developers and node runners.
No big deal. Amazon has blockchain-related services and a handful of patents pertaining to its digital currency inventions. No big deal either.
The write up says:
Google Cloud also announced it’s now indexing Solana data and adding it to its BigQuery data warehouse, a move that will “make it easier for the Solana developer ecosystem to access historical data.” The feature will launch in the first quarter of 2023, Mittal said. Mittal added that Google Cloud is bringing its credits program to “select startups in the Solana ecosystem” with up to $100,000 in Cloud Credits available for applicants.
Ah, more functionality.
What’s not in the write up? How about deanonymization functionality?
Stephen E Arnold, November 18, 2022
An Interesting NSO Related Action
November 9, 2022
In what sounds like the idea for a thriller/drama miniseries, The Times of Israel states that; “Former NSO CEO And Ex-Chancellor of Austria Establish New Cybersecurity Startup.” Sebastian Kurz, former Austrian chancellor, and ex-CEO of NSO Group Shalev Hulio established the new cybersecurity company Dream Security.
Hulio and Kurz formed Dream Security to protect critical infrastructures, such as energy, water, and oil facilities from cyber attacks. Dream Security will begin building a market in Europe. Kurz and Hulio raised $20 million in pre-seed funds from investors led by Dove Frances, who is an Israeli-American venture capitalist founder of the Group 11 investment firm. Other investors include entrepreneurs from the Israeli cybersecurity industry and early NSO Group investor Adi Shalev.
Founder Former Wayout Group CEO Gil Dolev will join Dream Security’s initial team.
Kurz and Hulio are concerned with infrastructures from their past work:
“Kurz told the publication that as Austrian chancellor, he ‘witnessed many attacks on governments as well as on manufacturing plants and energy installations, most of which were not published in the media. This has far-reaching implications for supply chains as well as regular energy supplies and public services such as water and hospitals.’
Hulio told Bloomberg he was leaving ‘the intelligence side, offensive side if you want, and move to the defensive side. We saw that the biggest challenge the cyber world is dealing with is critical infrastructure.’ He said the new company would focus on European markets ‘because I currently think that they have the biggest threats right now because of the geopolitical situation.’”
Both men’s reputations are covered with black marks . Kurz left politics because he was accused of a corruption scandal. At NSO Group, Hulio oversaw the development of the Pegasus spyware. Pegasus has been used by countries with poor human rights records to spy on “rabble rousers.” Apple and Facebook are pursuing lawsuits against NSO Group for breaking into their products and violating the terms of use. The European Union is investigating the use of Pegasus by its critics and the US Commerce Department blacklisted the company, then limited access to US components and technology.
Israel is also tightening restrictions on its cybersecurity companies. The number of countries that can buy Israeli cyber technology went from 100 down to 37.
It appears Dream Security is attempting to skirt Israeli restrictions by building a new company in Europe. The leaders are preaching they want to help people by protecting their infrastructures, but it would not be surprising if their plans were more nefarious.
Whitney Grace, November 9, 2022
DYOR and OSINT Vigilantes
November 7, 2022
DYOR is an acronym used by some online investigators for “do your own research.” The idea is that open source intelligence tools provide information that can be used to identify bad actors. Obviously once an alleged bad actor has been identified, that individual can be tracked down. The body of information gathered can be remarkably comprehensive. For this reason, some law enforcement, criminal analysts, and intelligence professionals have embraced OSINT or open source intelligence as a replacement for the human-centric methods used for many years. Professionals understand the limitations of OSINT, the intelware tools widely available on GitHub and other open source software repositories, and from vendors. The most effective method for compiling information and doing data analysis requires subject matter experts, sophisticated software, and access to information from Web sites, third-party data providers, and proprietary information such as institutional knowledge.
If you are curious about representative OSINT resources used by some professionals, you can navigate to www.osintfix.com and click. The site will display one of my research team’s OSINT resources. The database the site pulls from contains more than 3,000 items which we update periodically. New, useful OSINT tools and services become available frequently. For example, in the work for one of our projects, we came across a useful open source tool related to Tor relays. It is called OrNetStats. I mention the significance of OSINT because I have been doing lectures about online research. Much of the content in those lectures focuses on open source and what I call OSINT blind spots, a subject few discuss.
The article “The Disturbing Rise of Amateur Predator=Hunting Stings: How the Search for Men Who Prey on Underage Victims Became a YouTube Craze” unintentionally showcases another facet of OSINT. Now anyone can use OSINT tools and resources to examine an alleged bad actor, gather data about an alleged crime, and pursue that individual. The cheerleading for OSINT has created a boom in online investigations. I want to point out that OSINT is not universally accurate. Errors can creep into data intentionally and unintentionally. Examples range from geo-spoofing, identifying the ultimate owner of an online business, and content posted by an individual to discredit a person or business. Soft fraud (that is, criminal type actions which are on the edge of legality like selling bogus fashion handbags on eBay) is often supported by open source information which has been weaponized. One example is fake reviews of restaurants, merchants, products, and services.
I urge you to work through the cited article to get a sense of what “vigilantes” can do with open source information and mostly unfiltered videos and content on social media. I want to call attention to four facets of OSINT in the context of what the cited article calls “predator-hunting stings”:
First, errors and false conclusions are easy to reach. One example is identifying the place of business for an online service facilitating alleged online crime. Some services displace the place of business for some online actors in the middle of the Atlantic Ocean or on obscure islands with minimal technical infrastructure.
Second, information can be weaponized to make it appear that an individual is an alleged bad actor. Gig work sites allow anyone to spend a few dollars to have social media posts created and published. Verification checks are essentially non-existent. One doesn’t need a Russia- or China-system intelligence agency; one needs a way to hire part time workers usually at quite low rates. How does $5 sound.
Third, the buzz being generated about OSINT tools and techniques is equipping more people than ever before to become Sherlock Holmes in today’s datasphere. Some government entities are not open to vigilante inputs; others are. Nevertheless, hype makes it seems that anything found online is usable. Verification and understanding legal guidelines remain important. Even the most scrupulous vigilante may have difficulty getting the attention of some professionals, particularly government employees.
Fourth, YouTube itself has a wide range of educational and propagandistic videos about OSINT. Some of these are okay; others are less okay. Cyber investigators undergo regular, quite specific training in tools, sources, systems, and methods. The programs to which I have been exposed include references to legal requirements and policies which must be followed. Furthermore, OSINT – including vigilante-type inputs – have to be verified. In my lectures, I emphasize that OSINT information should be considered background until those data or the items of information have been corroborated.
What’s the OSINT blind spot in the cited article’s report? My answer is, “Verification and knowledge of legal guideless is less thrilling than chasing down an alleged bad actor.” The thrill of the hunt is one thing; hunting the right thing is another. And hunting in the appropriate way is yet another.
DYOR is a hot concept. It is easy to be burned.
Stephen E Arnold, November 7, 2022
What Is Better Than Biometrics Emotion Analysis of Surveillance Videos?
October 27, 2022
Many years ago, my team worked on a project to parse messages, determine if a text message was positive or negative, and flag the negative ones. Then of those negative messages, our job was to rank the negative messages in a league table. The team involved professionals in my lab in rural Kentucky, some whiz kids in big universities, a handful of academic experts, and some memorable wizards located offshore. (I have some memories, but, alas, these are not suitable for this write up.)
We used the most recent mechanisms to fiddle information from humanoid outputs. Despite the age of some numerical recipes, we used the latest and greatest. What surprised everyone is that our approach worked, particularly for the league table of the most negative messages. After reviewing our data, we formulated a simple, speedy way to pinpoint the messages which required immediate inspection by a person.
What was our solution for the deployable system?
Did we rely on natural language processing? Nope.
Did we rely on good old Reverend Bayes? Nope.
Did we rely on statistical analysis? Nope.
How did we do this? (Now keep in mind this was more than 15 years ago.)
We used a look up table of keywords.
Why? It delivered the league table of the most negative messages more than 85 percent of the time. The lookups were orders of magnitude faster than the fancy numerical recipes. The system was explainable. The method was extensible to second order negative messages with synonym expansion and, in effect, a second pass on the non-really negative messages. Yep, we crept into the 90 percent range.
I thought about this work for a company which went the way of most lavishly funded wild and crazy start ups from the go to years when I read “U.K. Watchdog Issues First of Its Kind Warning Against ‘Immature’ Emotional Analysis Tech.” This article addresses fancy methods for parsing images and other content to determine if a person is happy or sad. In reality, the purpose of these systems for some professional groups is to identify a potential bad actor before that individual creates content for the “if it bleeds, it leads” new organizations.
The article states:
The Information Commissioner’s Office, Britain’s top privacy watchdog, issued a searing warning to companies against using so-called “emotional analysis” tech, arguing it’s still “immature” and that the risks associated with it far outweigh any potential benefits.
You should read the full article to get the juicy details. Remember the text approach required one level of technology. We used a look up table because the magical methods were too expensive and too time consuming when measured against what was needed: Reasonable accuracy.
Taking videos and images, processing them, and determining if the individual in the image is a good actor or a bad actor, a happy actor or a sad actor, a nut job actor or a relative of Mother Teresa’s is another kettle of code.
Let’s go back to the question which is the title of this blog post: What Is Better Than Biometrics Emotion Analysis?
The answer is objective data about the clicks, dwell time, and types of indexed content an individual consumes. Lots of clicks translates to a signal of interest. Dwell time indicates attention. Cross correlate these data with other available information from primary sources and one can pinpoint some factoids that are useful in “knowing” about an individual.
My interest in the article was not the source article’s reminder that expectations for a technology are usually over inflated. My reaction was, “Imagine how useful TikTok data would be in identify individuals with specific predilections, mood changes plotted over time, and high value signals about an individual’s interests.”
Yep, just a reminder that TikTok is in a much better place when it comes to individual analysis than relying on some complicated methods which don’t work very well.
Practical is better.
Stephen E Arnold, October 27, 2022
A Data Taboo: Poisoned Information But We Do Not Discuss It Unless… Lawyers
October 25, 2022
In a conference call yesterday (October 24, 2022), I mentioned one of my laws of online information; specifically, digital information can be poisoned. The venom can be administered by a numerically adept MBA or a junior college math major taking short cuts because data validation is hard work. The person on the call was mildly surprised because the notion of open source and closed source “facts” intentionally weaponized is an uncomfortable subject. I think the person with whom I was speaking blinked twice when I pointed what should be obvious to most individuals in the intelware business. Here’s the pointy end of reality:
Most experts and many of the content processing systems assume that data are good enough. Plus, with lots of data any irregularities are crunched down by steamrolling mathematical processes.
The problem is that articles like “Biotech Firm Enochian Says Co Founder Fabricated Data” makes it clear that MBA math as well as experts hired to review data can be caught with their digital clothing in a pile. These folks are, in effect, sitting naked in a room with people who want to make money. Nakedness from being dead wrong can lead to some career turbulence; for example, prison.
The write up reports:
Enochian BioSciences Inc. has sued co-founder Serhat Gumrukcu for contractual fraud, alleging that it paid him and his husband $25 million based on scientific data that Mr. Gumrukcu altered and fabricated.
The article does not explain precisely how the data were “fabricated.” However, someone with Excel skills or access to an article like “Top 3 Python Packages to Generate Synthetic Data” and Fiverr.com or similar gig work site can get some data generated at a low cost. Who will know? Most MBAs math and statistics classes focus on meeting targets in order to get a bonus or amp up a “service” fee for clicking a mouse. Experts who can figure out fiddled data sets take the time if they are motivated by professional jealousy or cold cash. Who blew the whistle on Theranos? A data analyst? Nope. A “real” journalist who interviewed people who thought something was goofy in the data.
My point is that it is trivially easy to whip up data to support a run at tenure or at a group of MBAs desperate to fund the next big thing as the big tech house of cards wobbles in the winds of change.
Several observations:
- The threat of bad or fiddled data is rising. My team is checking a smart output by hand because we simply cannot trust what a slick, new intelware system outputs. Yep, trust is in short supply among my research team.
- Individual inspection of data from assorted open and closed sources is accepted as is. The attitude is that the law of big numbers, the sheer volume of data, or the magic of cross correlation will minimize errors. Sure these processes will, but what if the data are weaponized and crafted to avoid detection? The answer is to check each item. How’s that for a cost center?
- Uninformed individuals (yep, I am including some data scientists, MBAs, and hawkers of data from app users) don’t know how to identify weaponized data nor know what to do when such data are identified.
Does this suggest that a problem exists? If yes, what’s the fix?
[a] Ignore the problem
[b] Trust Google-like outfits who seek to be the source for synthetic data
[c] Rely on MBAs
[d] Rely on jealous colleagues in the statistics department with limited tenure opportunities
[e] Blink.
Pick one.
Stephen E Arnold, October 25, 2022
TikTok: Tracking Humanoids? Nope, Never, Ever
October 21, 2022
I read “TikTok Denies It Could Be Used to Track US Citizens.” Allegedly linked to the cheerful nation state China, TikTok allegedly asserts that it cannot, does not, and never ever thought about analyzing log data. Nope, we promise.
The article asserts:
The social media giant said on Twitter that it has never been used to “target” the American government, activists, public figures or journalists. The firm also says it does not collect precise location data from US users.
Here’s a good question: Has notion of persistent cookies, geospatial data, content consumption analytics, psychological profiling based on thematics have never jived with TikTok data at the Surveillance Soirée?
The answer is, according to the Beeb:
The firm [TikTok] also says it does not collect precise location data from US users. It was responding to a report in Forbes that data would have been accessed without users’ knowledge or consent. The US business magazine, which cited documents it had seen, reported that ByteDance had started a monitoring project to investigate misconduct by current and former employees. It said the project, which was run by a Beijing-based team, had planned to collect location data from a US citizen on at least two occasions.
Saying is different from doing in my opinion.
Based on my limited experience with online, would it be possible for a smart system with access to log data to do some high-value data analysis? Would it be possible to link the analytics’ output with a cluster of users? Would be possible to cross correlate data so that individuals with a predicted propensity of a desired behavior to be identified?
Of course not. Never. Nation states and big companies are fountains of truth.
TikTok. Why worry?
Stephen E Arnold, October 21, 2022
Cy4Gate Named As Big Player In AI Industry
October 21, 2022
There are famous industry awards: Academy Award, Golden Globe, Emmy, Pulitzer, Newbery Award, Caldecott Medal, Nobel Prize, Peabody Award, etc. These are associated with entertainment, science, and literature. Lesser-known industry awards are hardly heard of outside of their relevant fields, but they still earn bragging rights. Cy4Gate recently won bragging rights in AI: “Cy4Gate Mentioned As A Representative Provided In 2022 Gartner innovation Insight For Composite AI Report.”
Gartner is a renowned research company and anyone who gets a compliment from them is at the top of their game. Cy4Gate won recognition in AI as a “Representative Provider for Composite Artificial Intelligence solutions. Composite artificial intelligence is a combination of several machine learning algorithms (i.e.e deep neural network, natural language processing, computer vision, and speech recognition) to make big data analysis more effective and efficient without the need for relevant computation capabilities. Cy4Gate earned this notoriety for its years of development and research in AI applications.
“Since its establishment, Cy4gate has considered as decisive the use of AI in innovative ways, to ensure its products the ability to perform at excellent levels even in highly complex, uncertain and ambiguous contexts. Within these application areas, the enormous amount of data generated by the consistent increase of interconnected devices can be profitably used to adopt appropriate and timely decisions, and to reduce margins of error.”
Cy4Gate’s products, specializing in cyber security and intelligence, are believed to have a competitive advantage over their rivals. Other AI companies in the cyber security and intelligence field rely on single AI algorithms instead of combining them into composite artificial intelligence. Based on their advances and recognition, Cy4Gate established a new division of the company: the Data and Artificial Intelligence Center of Competence. It is part of the engineering department.
Whitney Grace, October 21, 2022
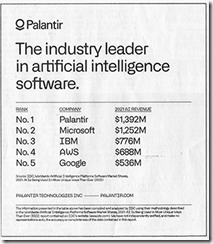
Palantir Technologies: Not Intelware, Now a Leader in Artificial Intelligence
September 27, 2022
I spotted this rather small advertisement in the Wall Street Journal dead tree edition on September 22, 2022. (I have been on the road and I had a stack of newspapers to review upon my return, so I may have the date off by a day or two. No big deal.)
Here’s the ad:
A couple of points jumped out. First, Palantir says in this smallish ad, “Palantir. The industry leader in artificial intelligence software.” That’s a very different positioning for the intelware centric company. I think Palantir was pitching itself a business intelligence solution and maybe a mechanism to identify fraud. Somewhere along the line there was a save the planet or save the children angle to the firm’s consulting-centric solutions.
For me, “consulting centric solutions” means that software (some open source, some whipped up by wizards) is hooked together by Palantir-provided or Palantir-certified engineers. The result is a dashboard with functionality tailored to a licensee’s problem. The money is in the consulting services for this knowledge work. Users of Palantir can fiddle, but to deliver real rock ‘em sock ‘em outputs, the bill by the hour folks are needed. This is no surprise to those familiar with migrations of software developed for one thing which is then, in a quest for revenues, is morphed into a Swiss Army knife and some wowza PowerPoint presentations and slick presentations at conferences. Feel free to disagree, please.
The second thing I noticed is that Palantir presents other leaders in smart software; specifically, the laggards at Microsoft, IBM, Amazon, and the Google. There are many ways to rank leaders. One distinction Palantir has it that it is not generating much of a return for those who bought the company’s stock since the firm’s initial public offering. On the other hand, the other four outfits, despite challenges, don’t have Palantir’s track record in the money department. (Yes, I know the core of Palantir made out for themselves, but the person I know in Harrod’s Creek who bought shares after the IPO: Not a good deal at this time.
The third thing is that Google, which has been marketing the heck out of its smart software is dead last in the Palantir list. Google and its estimable DeepMind outfit is probably not thrilled to be sucking fumes from Microsoft, IBM, and the outstanding product search solution provider Amazon. Google has articles flowing from Medium, technical papers explaining the magic of its AI/ML approach, and cheerleaders in academia and government waving pom poms for the GOOG.
I have to ask myself why? Here’s a breakdown of the notes I made after my team and I talked about this remarkable ad:
- Palantir obviously thinks its big reputation can be conveyed in a small ad. Palantir is perhaps having difficulty thinking objectively about the pickle the company’s sales team is in and wants to branch out. (Hey, doesn’t this need big ads?)
- Palantir has presented a ranking which is bound to irritate some at Amazon AWS. I have heard that some Palantir clients and some Palantir’s magic software runs on AWS. Is this a signal that Palantir wants to shift cloud providers? Maybe to the government’s go-to source of PowerPoint?
- Palantir may want to point out that Google’s Snorkeling and diversity methods are, in fact, not too good. Lagging behind a company like Palantir is not something the senior managers consider after a morning stretching routine.
Net net: This marketing signal, though really small, may presage something more substantive. Maybe a bigger ad, a YouTube video, a couple of TikToks, and some big sales not in the collectible business would be useful next steps. But the AI angle? Well, it is interesting.
Stephen E Arnold, September 27, 2022
The Cloud and Points of Failure: Really?
September 13, 2022
A professional affiliated with Syntropy points out one of my “laws” of online; namely, that centralization is inevitable. What’s interesting about “The Internet is Now So Centralized That One Company Can Break It” is that it does not explain much about Syntropy. In my opinion, there is zero information about the c9ompany. The firm’s Web site explains:
Unlocking the power of the world’s scientific data requires more than a new tool or method – it requires a catalyst for change and collaboration across industries.
The Web site continues:
We are committed to inspiring others around our vision — a world in which the immense power of a single source of truth in biomedical data propels us towards discoveries, breakthroughs and cures faster than ever before.
The company is apparently involved with Merck KGaA, which as I recall from my Pharmaceutical News Index days, is not too keen on sharing its intellectual property, trial data, or staff biographies. Also, the company has some (maybe organic, maybe more diaphanous) connection with Palantir Technologies. Palantir, an interesting search and retrieval company morphing into search based applications and consulting, is a fairly secretive outfit despite its being a publicly traded company. (The firm’s string of quarterly disappointments and its share price send a signal to some astute observers I think.)
But what’s in the article by individual identified at the foot of the essay as Domas Povilauskas, the top dog at Syntropy. Note that the byline for the article is Benzinga Contributor which is not particularly helpful.
Hmmm. What’s up?
The write up recycles the online leads to centralization notion. Okay. But centralization is a general feature of online information, and that’s not a particularly new idea either.
The author continues:
The problem with the modern Internet is that it is essentially a set of private networks run by individual internet service providers. Each has a network, and most connections occur between these networks…. Networks are only managed locally. Routing decisions are made locally by the providers via the BGP protocol. There’s no shared knowledge, and nobody controls the entire route of the connection. Using these public ISPs is like using public transport. You have no control over where it goes. Providers own the cables and everything else. In this system, there are no incentives for ISPs to provide a good service.
The set up of ISPs strikes me as a mix of centralization and whatever works. My working classification of ISPs and providers has three categories: Constrained services (Amazon-type outfits), Boundary Operators (the TOR relay type outfits), and Unconstrained ISPs and providers (CyberBunker-type organizations). My view is that this is the opposite of centralization. In each category there are big and small outfits, but 90 percent of the action follows Arnold’s Law of Centralization. What’s interesting is that in each category — for instance, boundary operators — the centralization repeats just on a smaller scale. AccessNow runs a conference. At this conference are many operators unknown by the general online user.
The author of the article says:
The only way to get a more reliable service is to pay ISPs a lot for high-speed private connections. That’s the only way big tech companies like Amazon run their data centers. But the biggest irony is that there is enough infrastructure to handle much more growth. 70% of Internet infrastructure isn’t utilized because nobody knows about these routes, and ISPs don’t have an excellent solution to monetize them on demand. They prefer to work based on fixed, predetermined contracts, which take a lot of time to negotiate and sign.
I think this is partially correct. As soon as one shifts from focusing on what appear to be legitimate online activities to more questionable and possibly illegal activities, evidence of persistent online services which are difficult for law enforcement to take down thrive. CyberBunker generated millions and required more than two years to knock offline and reign in the owners. There is more dimensionality in the ISP/provider sector than the author of the essay considers.
The knock-offline idea sounds good. One can point to the outages and the pain caused by Microsoft Azure/Microsoft Cloud, Google Cloud, Amazon, and others as points of weakness with as many vulnerabilities as a five-legged Achilles would have.
The reality is that the generalizations about centralization sound good, seem logical, and appear to follow the Arnold Law that says online services tend to centralization. Unfortunately new technologies exist which make it possible for more subtle approaches to put services online.
Plus, I am not sure how a company focused on a biomedical single source of truth fits into what is an emerging and diverse ecosystem of ISPs and service providers.
Stephen E Arnold, September 13, 2022